Defence in depth for web applications is something that not many companies apply even though the model itself is nothing new. Defence in depth refers to applying security controls across multiple layers, typically Data, Application, Host, Internal Network, Perimeter, Physical + Policies/Procedures/Awareness. Defence in depth is a principle of adding security in layers in order […]
Archives for March 2016
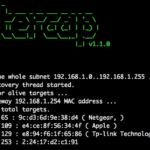
BetterCap – Modular, Portable MiTM Framework
BetterCAP is a powerful, modular, portable MiTM framework that allows you to perform various types of Man-In-The-Middle attacks against the network. It can also help to manipulate HTTP and HTTPS traffic in real-time and much more. BetterCap has some pretty impressive Spoofing abilities with multiple host discovery (just launch the tool and it will start […]
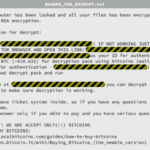
Mac OS X Ransomware KeRanger Is Linux Encoder Trojan
So there’s been a fair bit of noise this past week about the Mac OS X Ransomware, the first of its’ kind called KeRanger. It also happens to be the first popular Mac malware of any form for some time. It’s also a lesson to all the Apple fanbois that their OS is not impervious […]
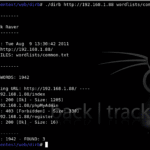
DIRB – Domain Brute-forcing Tool
DIRB is a Web Content Scanner AKA a domain brute-forcing tool. It looks for existing (and/or hidden) Web Objects, it works by launching a dictionary based attack against a web server and analysing the responses. What is DIRB? DIRB comes with a set of preconfigured attack word-lists for easy usage but you can use your […]
AuthMatrix for Burp Suite – Web Authorisation Testing Tool
AuthMatrix a web authorisation testing tool built as an extension to Burp Suite that provides a simple way to test authorisation in web applications and web services. With AuthMatrix, testers focus on thoroughly defining tables of users, roles, and requests for their specific target application upfront. These tables are displayed through the UI in a […]