The Veil-Framework is a collection of red team security tools that implement various attack methods focused on antivirus evasion and evading detection.
Antivirus ‘solutions’ don’t often catch the bad guys, but they do often catch pen-testing during assignment. This tool came about as a way to execute existing shellcode in a way that could evade AV engines without rolling a new backdoor each time.
It currently consists of:
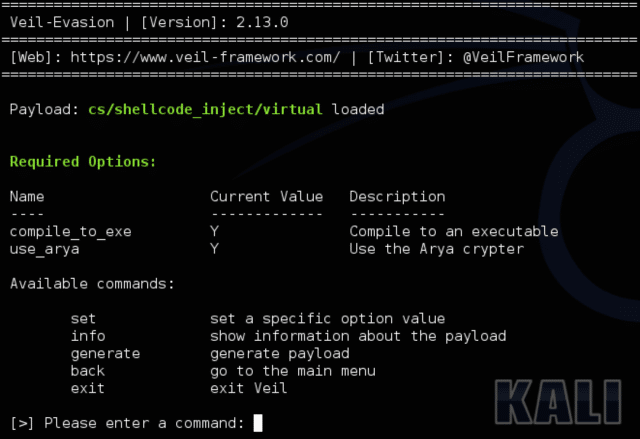
- Veil-Evasion: a tool to generate antivirus-evading payloads using a variety of techniques and languages
- Veil-Ordnance: a tool that can be used to quickly generate valid stager shellcode
- Veil-Catapult: a psexec-style payload delivery system that integrates Veil-Evasion
- Veil-Pillage: a modular post-exploitation framework that integrates Veil-Evasion
- Veil-PowerView: a powershell tool to gain network situational awareness on Windows domains
The Approach
Veil Evasion does its’ work by:
- Using an aggregation of various shellcode injection techniques across multiple languages
- Having a focus on automation, usability, and developing a true framework
- Using some shellcodeless Meterpreter stagers and “auxiliary” modules as well
One new payload is released each month with 30+ published payload modules.
You can download Veil Framework here (this is the ‘super’ project that will pull down the latest version of each tool):
Or read more here.
