Gophish is a phishing framework that makes the simulation of real-world phishing attacks very straight forwards. The idea behind gophish is simple – make industry-grade phishing training available to everyone.
There are various other similar tools available such as Simple Phishing Toolkit and sptoolkit Rebirth.
I wonder if this is the beginning of an emergence of portable, compiled Golang based security tools.
Features
- One-click Installation
- Standalone, portable binary with static assets
- Point-and-click Phishing
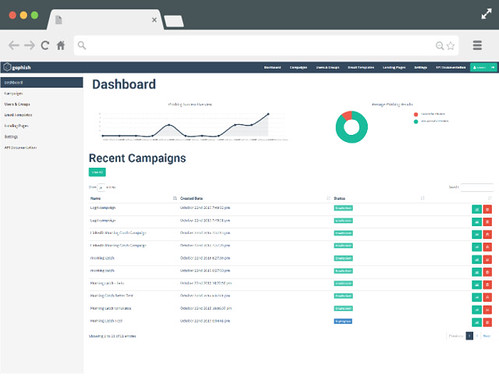
- Beautiful Web UI
- Automated Phishing campaigns
- RESTful API (JSON)
- Automated Training
- Open-Source
What’s New
Gopshish is pretty new and just hit the milestone of it’s first public beta release, so there are the main recent features:
- Added the timeline feature for campaign results
- Added default tracking to email templates
- Added additional events (such as when errors occur)
- Added the ability to access admin server/ phishing server over TLS
- Multiple UI fixes/tweaks (datatables, etc.)
- Added the ability to export results as CSV
You can download the User Guide here: Gopshish User Guide [PDF]
And you can download Gophish here:
Windows 64-Bit – gophish_windows_64bit.zip
Linux 64-Bit – gophish_linux_64bit.tar.gz
OSX 64-Bit – gophish_osx_64bit.zip
(If you’re still on a 32-Bit OS, you can go to the releases page to find a suitable download)
Or read more here.
