hping is a command-line oriented TCP/IP packet assembler/analyser. The interface is inspired to the ping unix command, but hping isn’t only able to send ICMP echo requests. It supports TCP, UDP, ICMP and RAW-IP protocols, has a traceroute mode, the ability to send files between a covered channel, and many other features.
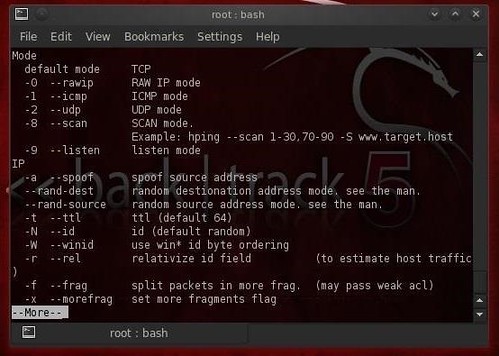
While hping was mainly used as a security tool in the past, it can be used in many ways by people that don’t care about security to test networks and hosts. It is a network tool able to send custom TCP/IP packets and to display target replies like ping do with ICMP replies. hping3 can handle fragmentation, and almost arbitrary packet size and content, using the command line interface.
What’s New
Since version 3, hping implements scripting capabilities, read the API.txt file under the /docs directory to learn more about it.
Basically hping uses the Tcl language as scripting language to write networking and security related applications, test suites, and software prototypes. To run hping in scripting mode just run it without arguments.
Features
- Firewall testing
- Advanced port scanning
- Network testing, using different protocols, TOS, fragmentation
- Manual path MTU discovery
- Advanced traceroute, under all the supported protocols
- Remote OS fingerprinting
- Remote uptime guessing
- TCP/IP stacks auditing
- hping can also be useful to students that are learning TCP/IP.
hping works on the following unix-like systems: Linux, FreeBSD, NetBSD, OpenBSD, Solaris, MacOs X, Windows.
There is a great tutorial to get started here: Getting started with hping3
You can download hping3 here:
Or read more here.
