FastIR Collector is Windows incident response tool that offers the possibility to extract classic artefacts such as memory dump, auto-started software, MFT, MBR, Scheduled tasks, Services and records the results in csv files. The tool can also perform smart acquisitions thanks to the filecatcher, certificate filtering or support of Yara rules.
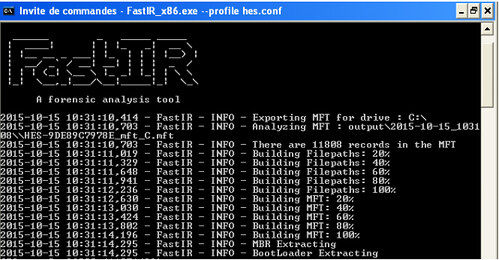
The first part of the name “Fast” was chosen because one of the prerequisite before the beginning of the development was to be able to perform forensic collections as quickly as possible. A standard collection (without filecatcher or dump) takes less than 1 minute 30 seconds on a Windows 7 system.
FastIR is designed to counter the growing size of hard drives, traditional forensics tools can take several hours to make a copy of the data and the volume of the data may be too large to make a reasonably speedy analysis.
Features
FastIR looks for various artefacts, including (but not limited to):
- Drive Identification – Archives all PE files not signed by Microsoft in Windows directories.
- Persistence Identification – Collects several persistence mechanisms.
- Named Pipes Identification – Rootkits often use named pipes to communication between components.
- Virtual File Systems – Collects & analyses Windows Prefetch files.
- Malware Identification – Using various artefacts and techniques.
- Process & Injection Identification – Able to identify various RATs, malware and rootkits from these artefacts.
The full documentation can be found here – FastIR_Documentation.pdf
Requirements
If you aren’t using the prebuilt exe:
- pywin32
- python WMI
- python psutil
- python yaml
- construct
- distorm3
- hexdump
- pytz
There is also a more extensive paper about the tool here: FastIR-Collector-on-advanced-threats_v1.5.pdf
You can download FastIR Collector here:
– FastIR_x64.exe
– FastIR_x86.exe
Or read more here
