Zarp is a network attack tool centred around the exploitation of local networks. This does not include system exploitation, but rather abusing networking protocols and stacks to take over, infiltrate, and knock out. Sessions can be managed to quickly poison and sniff multiple systems at once, dumping sensitive information automatically or to the attacker directly.
Various sniffers are included to automatically parse usernames and passwords from various protocols, as well as view HTTP traffic and more. DoS attacks are included to knock out various systems and applications. These tools open up the possibility for very complex attack scenarios on live networks quickly, cleanly, and quietly.
Features
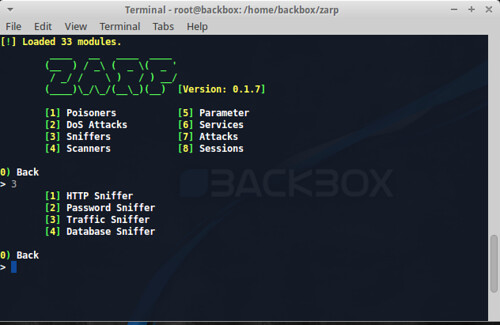
zarp has around 30+ modules grouped into categories of attack and has multiple functionalities under each group:
- Poisoners
- Denial of Service
- Sniffers
- Scanners
- Services
- Parameter
- Attacks
Installation
zarp is intended to be as dependency-free as possible. When available, zarp has opted to use pure or native Python implementations over requiring or importing huge libraries. Even as such, zarp requires the following to run:
- Linux
- Python 2.7.x
- Scapy (packaged with zarp)
It is also recommended that user’s have the following installed for access to specific modules:
- airmon-ng suite (for all your wireless cracking needs)
- tcpdump
- libmproxy (packaged with zarp)
- paramiko (SSH service)
- nfqueue-bindings (packet modifier)
Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 |
./zarp.py --help [!] Loaded 34 modules. ____ __ ____ ____ (__ ) / _\ ( _ \( _ ' / _/ / \ ) / ) __/ (____)\_/\_/(__\_)(__) [Version: 0.1.5] usage: zarp.py [-h] [-q FILTER] [--update] [--wap] [--ftp] [--http] [--smb] [--ssh] [--telnet] [-w] [-s] [--service-scan] optional arguments: -h, --help show this help message and exit -q FILTER Generic network sniff --update Update Zarp Services: --wap Wireless access point --ftp FTP server --http HTTP Server --smb SMB Service --ssh SSH Server --telnet Telnet server Scanners: -w Wireless AP Scan -s Network scanner --service-scan Service scanner run (r) - Run the selected module info - Display module information |
The Future
The long-term goal of this network attack tool zarp is to become the master command center of a network; to provide a modular, well-defined framework that provides a powerful overview and in-depth analysis of an entire network. This will come to light with the future inclusion of a web application front-end, which acts as the television screen, whereas the CLI interface will be the remote. This will provide network topology reports, host relationships, and more. zarp aims to be your window into the potential exploitability of a network and its hosts, not an exploitation platform itself; it is the manipulation of relationships and trust felt within local intranets.
You can download zarp here:
Or read more here.
