SpiderFoot is an open source intelligence automation tool. Its goal is to automate the process of gathering intelligence about a given target, which may be an IP address, domain name, hostname or network subnet.
SpiderFoot can be used offensively, i.e. as part of a black-box penetration test to gather information about the target or defensively to identify what information your organisation is freely providing for attackers to use against you.
Purpose
There are three main areas where SpiderFoot can be useful:
- If you are a pen-tester, SpiderFoot will automate the reconnaisance stage of the test, giving you a rich set of data to help you pin-point areas of focus for the test.
- Understand what your network/organisation is openly exposing to the outside world. Such information in the wrong hands could be a significant risk.
- SpiderFoot can also be used to gather threat intelligence about suspected malicious IPs you might be seeing in your logs or have obtained via threat intelligence data feeds.
Features
SpiderFoot has plenty of features, including the following:
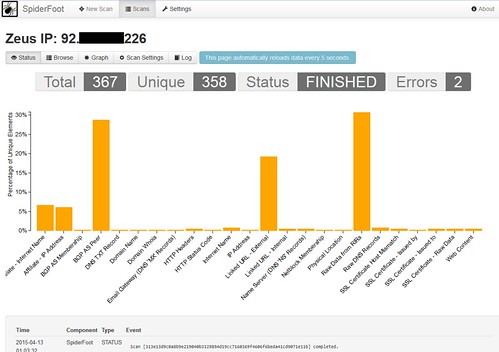
- Utilises a lot of different data sources; over 40 so far and counting, including SHODAN, RIPE, Whois, PasteBin, Google, SANS and more.
- Designed for maximum data extraction; every piece of data is passed on to modules that may be interested, so that they can extract valuable information. No piece of discovered data is saved from analysis.
- Runs on Linux and Windows. And fully open-source so you can fork it on GitHub and do whatever you want with it.
- Visualisations. Built-in JavaScript-based visualisations or export to GEXF/CSV for use in other tools, like Gephi for instance.
- Web-based UI. No cumbersome CLI or Java to mess with. Easy to use, easy to navigate. Take a look through the gallery for screenshots.
- Highly configurable. Almost every module is configurable so you can define the level of intrusiveness and functionality.
- Modular. Each major piece of functionality is a module, written in Python. Feel free to write your own and submit them to be incorporated!
- SQLite back-end. All scan results are stored in a local SQLite database, so you can play with your data to your heart’s content.
- Simultaneous scans. Each footprint scan runs as its own thread, so you can perform footprinting of many different targets simultaneously.
You can download SpiderFoot 2.6.0 here:
Windows – SpiderFoot-2.6.0-w32.zip
Linux – spiderfoot-2.6.0-src.tar.gz
Or read more here.
