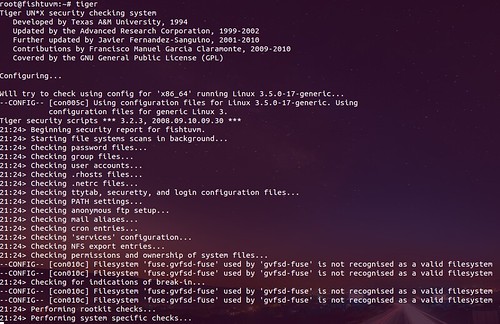
Tiger is a Unix security audit tool that can be use both for auditing and as an intrusion detection system. It supports multiple Unix platforms and it is free and provided under a GPL license. Unlike other tools, Tiger needs only POSIX tools and is written entirely in shell language.
Tiger has some interesting features that merit its resurrection, including a modular design that is easy to expand, and its double edge, it can be used as an audit tool and a host intrusion detection system tool.
Free Software intrusion detection is currently going many ways, from network IDS (with Snort), to the kernel (LIDS, or SNARE for Linux and Systrace for OpenBSD, for example), not mentioning file integrity checkers (many of these: aide, integrit, samhain, tripwire…) and logcheckers (even more of these, check the Log Analysis pages). But few of them focus on the host-side of intrusion detection fully.
Tiger complements these tools and also provides a framework in which all of them can work together. Tiger is not a logchecker, nor it focused in integrity analysis. It does “the other stuff”, it checks the system configuration and status. Read the manpage for a full description of checks implemented in Tiger. A good example of what Tiger can do is, for example, check_findeleted, a module that can determine which network servers running in a system are using deleted files (because libraries were patched during an upgrade but the server’s services not restarted).
There are other similar tools, but most of them focus on privilege escalation:
– LinEnum – Linux Enumeration & Privilege Escalation Tool
– Lynis v1.6.0 Released For Download – Linux Security Auditing Tool
– unix-privesc-check – Unix/Linux User Privilege Escalation Scanner
You can download Tiger here:
Or read more here.
