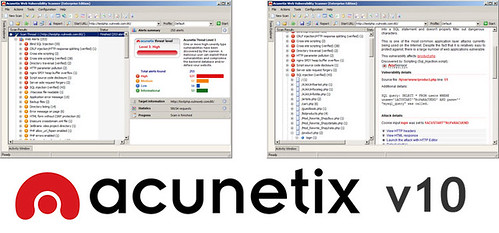
Acunetix WVS 10 Released
Acunetix, the pioneer in automated web application security software, has announced the release of version 10 of its Vulnerability Scanner. New features are designed to prevent the risk of hacking for all customers; from small businesses up to large enterprises, including WordPress users, web application developers and pen testers.
With the number of cyber-attacks drastically up in the last year and the cost of breaches doubling, never has limiting this risk been such a high priority and a cost-effective investment. The 2015 Information Security Breaches Survey from PWC found 90% of large organisations had suffered a breach and average costs have escalated to over £3m per breach, at the higher end.
“It’s a sad fact that today the odds are that your business has already been breached, perhaps multiple times. Don’t let cyber-criminals drive your web app security strategy. Proactively identify security exploits before criminals do and take back control,” said Nick Galea, CEO, Acunetix.
The areas of a website which are most likely to be attacked and are prone to vulnerabilities are those areas that require a user to login. Therefore the latest version of Acunetix vastly improves on its ‘Login Sequence Recorder’ which can now navigate multi-step authenticated areas automatically and with ease. It crawls at lightning speed with its ‘DeepScan’ crawling engine now analyzing web applications developed using both Java Frameworks and Ruby on Rails. Version 10 also improves the automated scanning of RESTful and SOAP-based web services and can now detect over 1200 vulnerabilities in WordPress core and plugins.
“Acunetix maintains its lead in cutting-edge web application technologies. By re-engineering the ‘Login Sequence Recorder’ from the ground up and baking-in support for external tools, we have extended the scanner’s reach into web applications, further bridging the gap between manual and automated security testing,” added Nick Galea.
New in WVS 10
- ‘Login Sequence Recorder’ has been re-engineered from the ground-up to allow restricted areas to be scanned entirely automatically.
- Now tests for over 1200 WordPress-specific vulnerabilities in the WordPress core and plugins.
- Acunetix WVS Crawl data can be augmented using the output of: Fiddler .saz files, Burp Suite saved items, Burp Suite state files, HTTP Archive (.har) files, Acunetix HTTP Sniffer logs, Selenium IDE Scripts.
- Improved support for Java Frameworks (Java Server Faces [JSF], Spring and Struts) and Ruby on Rails.
- Increased web services support for web applications which make use of WSDL based web-services, Microsoft WCF-based web services and RESTful web services.
- Ships with a malware URL detection service, which is used to analyse all the external links found during a scan against a constantly updated database of Malware and Phishing URLs.
Automated scanning of restricted areas
Latest automation functionality makes Acunetix not only even easier to use, but gives better peace of mind through ensuring the entire website is scanned. Restricted areas, especially user login pages, make it more difficult for a scanner to access and often required manual intervention. The Acunetix “Login Sequence Recorder” overcomes this, having been significantly improved to allow restricted areas to be scanned completely automatically. This includes the ability to scan web applications that use Single Sign-On (SSO) and OAuth-based authentication. With the recorder following user actions rather than HTTP requests, it drastically improves support for anti-CSRF tokens, nonces or other one-time tokens, which are often used in restricted areas.
Top dog in WordPress vulnerability detection
With WordPress sites having exceeded 74 million in number, a single vulnerability found in the WordPress core, or even in a plugin, can be used to attack millions of individual sites. The flexibility of being able to use externally developed plugins leads to the development of even more vulnerabilities. Acunetix v10 now tests for over 1200 WordPress-specific vulnerabilities, based on the most frequently downloaded plugins, while still retaining the ability to detect vulnerabilities in custom built plugins. No other scanner on the market can detect as many WordPress vulnerabilities.
Support for various development architectures and web services
Many enterprise-grade, mission critical applications are built using Java Frameworks and Ruby on Rails. Version 10 has been engineered to accurately crawl and scan web applications built using these technologies. With the increase in HTML5 Single Page Applications and mobile applications, web services have become a significant attack vector. The new version improves support for SOAP-based web services with WSDL and WCF descriptions as well as automated scanning of RESTful web services using WADL definitions. Furthermore, version 10, introduces dynamic crawl pre-seeding by integrating with external, third-party tools including Fiddler, Burp Suite and the Selenium IDE to enhance Business Logic Testing and the workflow between Manual Testing and Automation.
Detection of Malware and Phishing URLs
Acunetix WVS 10 will ship with a malware URL detection service, which is used to analyse all the external links found during a scan against a constantly updated database of Malware and Phishing URLs. The Malware Detection Service makes use of the Google and Yandex Safe Browsing Database.
A trial version can be downloaded from:
