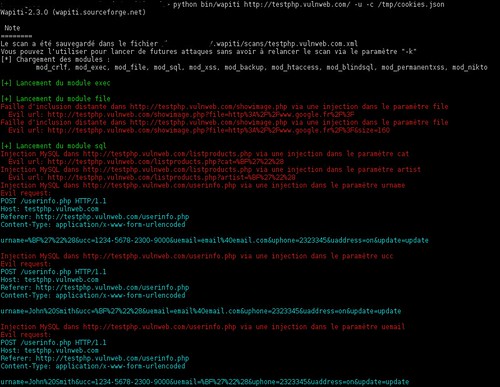
Wapiti is a web application vulnerability scanner, it allows you to audit the security of your web applications. It performs “black-box” scans, i.e. it does not study the source code of the application but will scans the web pages of the deployed web application, looking for scripts and forms where it can inject data.
Once it gets this list, Wapiti acts like a fuzzer, injecting payloads to see if a script is vulnerable.
We first wrote about Wapiti WAYYY back in 2006 – Wapiti – Web Application Scanner / Black-box testing. It’s come a long way since then, but there doesn’t seem to be much active development since 2013 – which is a shame as it’s a good tool.
Wapiti can detect the following vulnerabilities :
- File disclosure (Local and remote include/require, fopen, readfile…)
- Database Injection (PHP/JSP/ASP SQL Injections and XPath Injections)
- XSS (Cross Site Scripting) injection (reflected and permanent)
- Command Execution detection (eval(), system(), passtru()…)
- CRLF Injection (HTTP Response Splitting, session fixation…)
- XXE (XmleXternal Entity) injection
- Use of know potentially dangerous files (thanks to the Nikto database)
- Weak .htaccess configurations that can be bypassed
- Presence of backup files giving sensitive information (source code disclosure)
Features
- Generates vulnerability reports in various formats (HTML, XML, JSON, TXT…)
- Can suspend and resume a scan or an attack
- Can give you colors in the terminal to highlight vulnerabilities
- Different levels of verbosity
- Fast and easy way to activate/deactivate attack modules
- Adding a payload can be as easy as adding a line to a text file
- Supports both GET and POST HTTP methods for attacks
- It also supports multipart and can inject payloads in filenames (upload)
- Display a warning when an anomaly is found (for example 500 errors and timeouts)
- Makes the difference beetween permanent and reflected XSS vulnerabilities.
You can download Wapiti v2.3.0 here:
Windows – wapiti-2.3.0-win32-standalone.zip
Linux – wapiti-2.3.0.tar.gz
Or read more here.

poto says
Why mention the tool if it was abandoned?
Feeling nostalgic again?
Darknet says
Because it’s still good, and there’s been a lot of improvements since our last post about it in 2006. Perhaps with some attention, they might start development again..