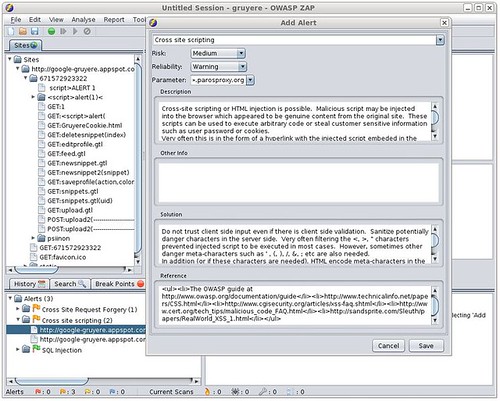
The OWASP Zed Attack Proxy (ZAP) is an easy to use integrated penetration testing tool for finding vulnerabilities in web applications. It is designed to be used by people with a wide range of security experience and as such is ideal for developers and functional testers who are new to penetration testing as well as being a useful addition to an experienced pen testers toolbox.
With its automated scanner and powerful REST API, ZAP fits seamlessly into your continuous integration environment, allowing you to automate the finding of common issues while you’re still in development.
It’s classified as a flagship project for OWASP meaning it’s mature and has demonstrated strategic value to OWASP and application security as a whole. It’s also fully translated into 25 different languages, which is more than a lot of commercial/enterprise tools.
Alternatives to ZAP would be:
– Fiddler – Web Debugging Proxy For HTTP(S)
– Burp Suite Free Edition v1.4 – Web Application Security Testing Tool
– Charles Web Debugging Proxy – HTTP Monitor & Reverse Proxy
We have written about ZAP before, when it first hit v1.0 back in 2010 and again when they had a major update in 2011.
Features
- Open source
- Cross platform
- Easy to install
- Completely free
- Ease of use a priority
- Comprehensive help pages
- Fully internationalized
- Translated into a dozen languages
- Community based, with involvement actively encouraged
- Under active development by an international team of volunteers
Functionality
- Intercepting proxy
- Traditional and AJAX spiders
- Active scanner
- Passive scanner
- Forced Browsing
- Fuzzer
- Dynamic SSL certificates
- Smart card support
- Web sockets support
- Authentication and session support
- Powerful REST based API
- Support for a wide range of scripting languages
- Automatic updating option
- Integrated and growing marketplace of add-ons
When used as a proxy server it allows the user to manipulate all of the traffic that passes through it, including traffic using https. It can also run in a ‘daemon’ mode which is then controlled via a REST Application programming interface.
This cross-platform tool is written in Java and is available in all of the popular operating systems including Microsoft Windows, Linux and Mac OS X.
You can download ZAP here:
Windows – ZAP_2.4.0_Windows.exe
Linux – ZAP_2.4.0_Linux.tar.gz
Mac OS X – ZAP_2.4.0_Mac_OS_X.dmg
There is also a Docker image available here.
Or read more here.
