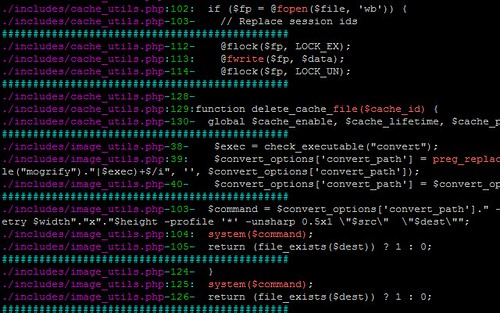
Graudit is a simple script and signature sets that allows you to find potential security flaws in source code using the GNU utility grep. It’s comparable to other static analysis applications and source code auditing tool sets like RATS, SWAAT and flaw-finder while keeping the technical requirements to a minimum and being very flexible.
You can find a full selection of code auditing tools here.
Usage
Graudit supports several options and tries to follow good shell practices. For a list of the options you can run graudit -h or see below. The simplest way to use graudit is;
|
1 |
graudit <options> /path/to/scan |
The following options are available:
|
1 2 3 4 5 6 7 8 9 10 11 |
-A scan ALL files -c <num> number of lines of context to display, default is 2 -d <db> database to use -h prints a short help text -i case in-sensitive search -l lists databases available -L vim friendly lines -v prints version number -x exclude these files -z supress colors -Z high contrast colors |
Databases
Graudit uses extended regular expressions (POSIX) as it’s signatures and comes with several databases ready for use. You can extend the existing databases or make your own if you require additional signatures.
- All is a combined database of all the databases listed below
- ASP offers basic auditing support for the Active Server Pages languages
- C offers support for the C programming language
- Default is aimed at finding low hanging fruit. It contains generic rules that should match common vulnerabilites in several languages. However, in order to find additional vulnerabilities for a specific language you should use the language specific databases.
- Dotnet offers basic dot net support
- JSP basic JSP support.
- Other looks for source comments that could indicate problems
- Perl basic support for perl
- PHP tracks user input and function calls
- Python basic python support
You can download Graudit v1.9 here:
Or read more here.
