Acunetix have announced that they are extending their current free offering of the network security scan, part of their cloud-based web and network vulnerability scanner. Those signing up for a trial of the online version of Acunetix vulnerability scanner will now be able to scan their perimeter servers for network security issues on up to 3 targets with no expiry.
In addition, existing Acunetix customers will also be able to double up on their current license-based quota of scan targets by adding the same amount of network scans. i.e a 25 scan target license can now make use of an extra 25 network-only scan targets for free.
An analysis of scans performed over the past year following the launch of Acunetix Vulnerability Scanner (online version) show that on average 50% of the targets scanned have a medium or high network security vulnerability. It’s worrying that in the current cybersecurity climate, network devices remain vulnerable to attack. The repercussions of a vulnerable network are catastrophic as seen in some recent, well publicised Lizard Squad attacks, the black hat hacking group, mainly known for their claims of DoS attacks.
“Acunetix secure the websites of some of the biggest global enterprises, and with our online vulnerability scanner we are not only bringing this technology within reach of many more businesses but we are also providing free network security scanning technology to aid smaller companies secure their network,” said Nick Galea, CEO of Acunetix.
How Acunetix keeps perimeter servers secure
A network security scan checks the perimeter servers, locating any vulnerabilities in the operating system, server software, network services and protocols. Acunetix network security scan uses the OpenVAS database of network vulnerabilities and scans for more than 35,000 network level vulnerabilities. A network scan is where vulnerabilities such as Shellshock, Heartbleed and POODLE are detected, vulnerabilities which continue to plague not only web servers but also a large percentage of other network servers.
You can find our review here:
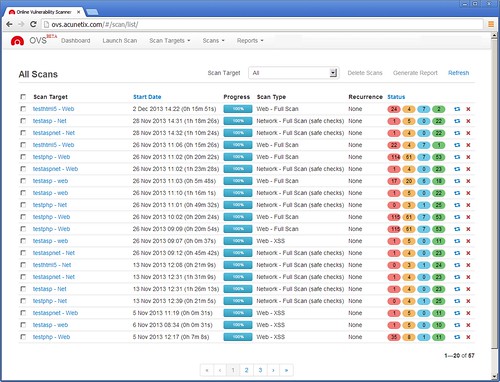
Acunetix OVS Review (Online Vulnerability Scanner)
A network scan will also:
- Detect misconfigurations and vulnerabilities in OS, server applications, network services, and protocols
- Assess security of detected devices (routers, hardware firewalls, switches and printers)
- Scan for trojans, backdoors, rootkits, and other malware that can be detected remotely
- Test for weak passwords on FTP, IMAP, SQL servers, POP3, Socks, SSH & Telnet
- Check for DNS server vulnerabilities such as Open Zone Transfer, Open Recursion and Cache Poisoning
- Test FTP access such as anonymous access potential and a list of writable FTP directories
- Check for badly configured Proxy Servers, weak SNMP Community Strings, weak SSL ciphers and many other security weaknesses.
About Acunetix
Acunetix is the market leader in web application security technology, founded to combat the alarming rise in web attacks. Its products and technologies are the result of a decade of work by a team of highly experienced security developers. Acunetix’ customers include the U.S. Army, KPMG, Adidas and Fujitsu. More information can be found at www.acunetix.com.
Register for a free trial and start scanning here:
