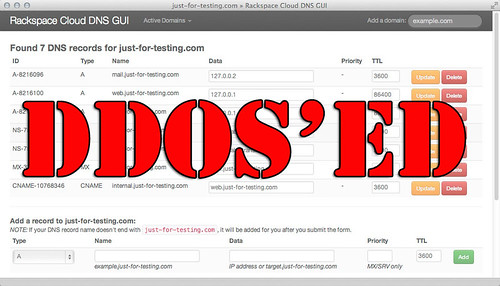
So Rackspace has just recovered from a major DNS DDoS attack which rendered some domains inaccessible for over 11 hours. It seems to have been a fairly frequent occurrence lately with Namecheap also undergoing several attacks against its DNS infrastructure.
I got affected again recently on December 18th when they were hit with a massive attack: DDoS Attack against Default DNS System V2
This wasn’t the only attack with a large portion of the Internt being effected back in February when Namecheap DNS system underwent a heavy and sustained DDoS attack: Namecheap Is In The Middle Of A DDoS Attack.
Rackspace says it has recovered from a nasty distributed denial of service attack that it says may have seen “a portion of legitimate traffic to our DNS infrastructure … inadvertently blocked.”
The trouble started just before lunchtime on Monday, US central time, and persisted until 11 hours later.
Over on the company’s Google+ page Rackspace warned of “intermittent periods of latency, packet loss, or connectivity failures when attempting to reach rackspace.com or subdomains within rackspace.com.”
The company’s status report later confirmed it had “… identified a UDP DDoS attack targeting the DNS servers in our IAD, ORD, and LON data centers [North Virigina, Chicago and London]. As a result of this issue, authoritative DNS resolution for any new request to the DNS servers began to fail in the affected data centers. In order to stabilize the issue, our teams placed the impacted DNS infrastructure behind mitigation services.
Several other services have been hit with heavy, sustained DDoS attacks for no apparent reason including SaaS services like Dropbox which got taken offline.
In this instance (as usual) there doesn’t seem to be any reason so far, perhaps extortion? Gaming services are frequent targets with Steam, Xbox Live and PSN all having been taken offline previously by DDoS attacks.
This service is designed to protect our infrastructure, however, due to the nature of the event, a portion of legitimate traffic to our DNS infrastructure may be inadvertently blocked. Our teams are actively working to mitigate the attack and provide service stability.”
Rackspace is now confident things are back in order, as it has blacklisted DNS servers that were “sending both legitimate and DDoS traffic to Rackspace”. Users may not be entirely out of the woods, as its most recent update says “If you continue to experience adverse impact, please reach out to your support teams and provide trace route information for further investigations.”
A full root cause analysis of the incident is under way.
It can be really serious too, earlier this year Code Spaces was put out of business by a sustained DDoS attack which turned into an intrusion, extortion and eventual deletion of their entire business.
It’ll be interesting to see if any reason comes out for this Rackspace attack, but with the power of botnets now – it might just be for no reason at all.
A recent survey has shown that DNS attacks are putting organizations at risk – so yah, serious business.
Source: The Register
