Isowall is a mini-firewall that allows you to completely isolate a device from the local network. This is for allowing infected machines Internet access, but without endangering the local network.
Building
This project depends upon libpcap, and of course a C compiler.
On Debian, the following should work:
|
1 2 3 4 |
# apt-get install git gcc make libpcap-dev # git clone https://github.com/robertdavidgraham/isowall # cd isowall # make |
This will put the binary isowall in the local isowall/bin directory.
This should also work on Windows, Mac OS X, xBSD, and pretty much any operating system that supports libpcap.
Running
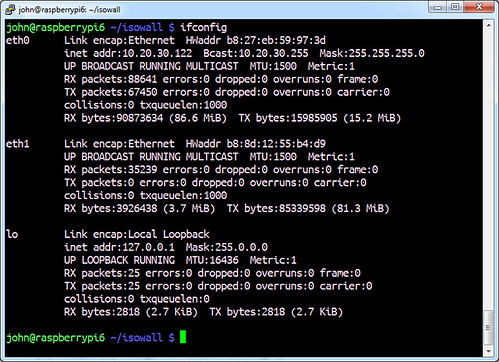
First, setup a machine with three network interfaces.
The first network interface (like eth0) will be configured as normal, with a TCP/IP stack, so that you can SSH to it.
The other two network interfaces should have no TCP/IP stack, no IP address, no anything. This is the most important configuration step, and the most common thing you’ll get wrong. For example, the DHCP software on the box may be configured to automatically send out DHCP requests on these additional interfaces. You have to go fix that so nothing is bound to these interfaces.
To run, simply type:
|
1 |
# ./bin/isowall --internal eth1 --external eth2 -c xxxx.conf |
Configuration
The following shows a typical configuration file
|
1 2 3 4 5 6 7 8 9 10 11 12 |
internal = eth1 internal.target.ip = 10.0.0.129 internal.target.mac = 02:60:8c:37:87:f3 external = eth2 external.router.ip = 10.0.0.1 external.router.mac = 66:55:44:33:22:11 allow = 0.0.0.0/0 block = 192.168.0.0/16 block = 10.0.0.0/8 block = 224.0.0.0-255.255.255.255 |
You can download isowall here:
Or read more here – the author can be found on Twitter here @erratarob.

Mark Edw5he mosorthy says
Whilst isowall sounds like an interesting project, surely the most effective way of isolating a computer from a network, is to disconnect all nic connections (including any ethernet cables and / or wireless connections)
Darknet says
This is for when that machine needs an Internet connection (like a Honeypot, or malware that connects outwards that you want to packet sniff/analyse) but you want to isolate it from the rest of the network so it can’t hop between machines.