masscan is the fastest TCP port scanner, a really fast network scanner. It can scan the entire Internet in under 6 minutes, transmitting 10 million packets per second. What is masscan – The Fast Network Scanner? It produces results similar to nmap, the most famous port scanner. Internally, it operates more like scanrand, unicornscan, and […]
Archives for September 2014
Everything You NEED To Know About Shellshock Bug In BASH
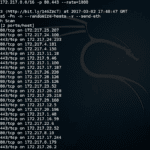
Shellshock (CVE-2014-6271) the bug in BASH is causing havoc on the Internet this week, as far as I’m concerned it’s a bit overstated – seriously how many people are still using cgi scripts? None I hope. I do suspect though a lot of shared hosts might get owned by this as most commercial control panel […]
drozer – The Leading Security Testing Framework For Android
drozer (formerly Mercury) is the leading security testing framework for Android. drozer allows you to search for security vulnerabilities in apps and devices by assuming the role of an app and interacting with the Dalvik VM, other apps’ IPC endpoints and the underlying OS. drozer provides tools to help you use, share and understand public […]
CloudFlare Introduces SSL Without Private Key
Handing over your private key to a cloud provider so they can terminate your SSL connections and you can work at scale has always been a fairly contentious issue, a necessary evil you may say. As if your private key gets compromised, it’s a big deal and without it (previously) there’s no way a cloud […]
tinfoleak – Get Detailed Info About Any Twitter User
tinfoleak is basically an OSINT tool for Twitter, there’s not a lot of stuff like this around – the only one that comes to mind in fact is creepy – Geolocation Information Aggregator. tinfoleak is a simple Python script that allow to obtain: basic information about a Twitter user (name, picture, location, followers, etc.) devices […]