Hack.me is a FREE, community based project powered by eLearnSecurity. The community allows you to build, host and share vulnerable web application code for educational and research purposes.
It aims to be the largest collection of “runnable” vulnerable web applications, code samples and CMS’s online. The platform is available without any restriction to any party interested in Web Application Security: students, universities, researchers, penetration testers and web developers.
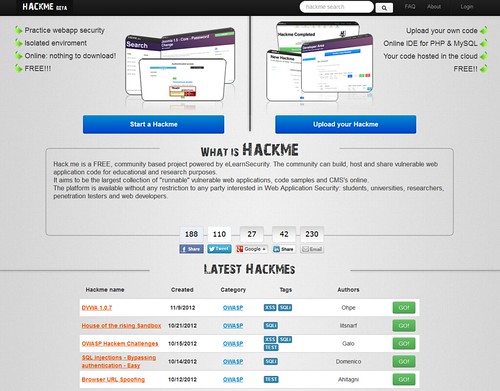
Features
- Upload your own code
- Online IDE for PHP & MySQL
- Your code hosted in the cloud
- FREE!!
- Practice webapp security
- Isolated enviroment
- Online: nothing to download!
Safety
Every time you run a new Hackme the site will initiate a new sandbox for you. You will get isolated access to it so that you will always know that the application is safe for you to use. No other students can add malware or exploits in your sandbox. This ensures 99% safety.
What about the 1%? While the team makes the best effort to moderate every and each new web app uploaded on Hack.me, chances are that something can and will slip through. If you are not 100% comfortable to trust us or the Hackme developer, please just run new Hackmes from a virtual machine or from a non production OS.
We have written about a variety of web apps where you can practice your hack-fu such as:
So head over to hack.me and see what you think:
