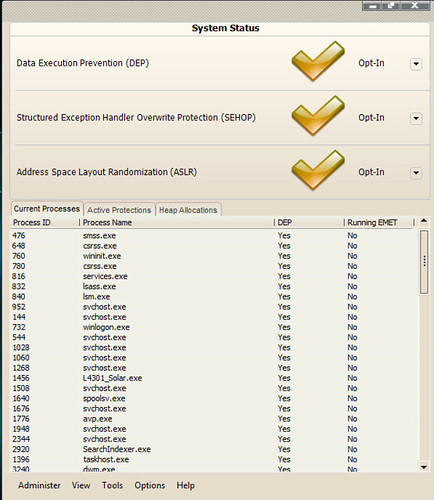
We published an article about Microsoft Enhanced Mitigation Evaluation Toolkit (EMET) when it came out back in June 2011.
The Native GUI for EMET is in .NET and there are some situations or restricted environments where you may be unable to install .NET or just simple don’t want to use it.
This is where this third-party graphical interface for the Enhanced Mitigation Experience Toolkit comes in, it has no dependence on .NET and will work fine in environments without that capability.
You can download EMET GUI here:
Or read more here.
