Introduction
Yes, there’s another new kid on the block when it comes to penetration testing training, this course is known as CODENAME: Samurai Skills by Ninja-Sec. I’m not going to go and compare this to any other course out there as I think there’s a place for all of them, and they all have pros and cons.
The author is one Mohamed Ramadan who does in fact know what he’s talking about, for a sample of his writing outside of this course-ware you can check here:
How Hackers Target and Hack Your Site
The course is marketed under the brand Ninja-Sec:

The main focus of this course is to teach you the following skills:
- Gather Information Intelligence
- Find Web Applications and System Security Vulnerabilities
- Scan Your Target Stealthily
- Exploit Web Applications and System Vulnerabilites
- Conduct Real World Client Side Attacks
- Conduct Tactical Post Exploitation on Windows and Linux Systems
- Develop Windows Exploits
They themselves consider this a medium level course and are promising to come out with a more advanced course soon. I consider this course a good introduction to pen testing or as a good supplement to other more hardcore courses (like OSCP).
There’s a fair mix of introductory material and slides + ample video which walks you through the slides and shows hands on demonstrations.
The Course
The course covers 8 modules:
- Module 1: Solid Introduction to Penetration Testing
- Module 2: Real World Information Intelligence Techniques
- Module 3: Scanning and Vulnerability Assessment
- Module 4: Network Attacking Techniques
- Module 5: Windows – Unix Attacking Techniques
- Module 6: Windows – Unix Post-exploitation Techniques
- Module 7: Web Exploitation Techniques
- Module 8: Windows Exploit Development
Each module contains a ‘book’ – which is basically a set of presentation slides and video content – the length of the video varies greatly between chapters (the shortest is the introduction at 35 minutes and the longest is almost 5 hours for module 7).
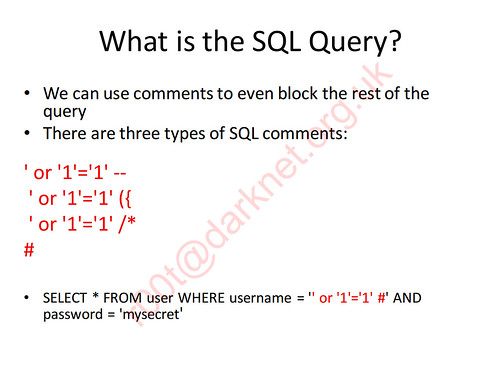
The presentation slides generally give some introductory material, then run through the relevant subject in a fair amount of depth. Here’s an example of a slide:
It runs all the way from a foundation introduction to penetration testing to a quite advanced module about Windows exploit development.
Here’s a sample of the video material, also about SQL Injection:
The course runs through a great variety of tools and techniques, from old to new. It’s actually a great companion for the Darknet site, as we have written about most of the tools featured in the course – but we haven’t published many tutorials on how to actually use them.
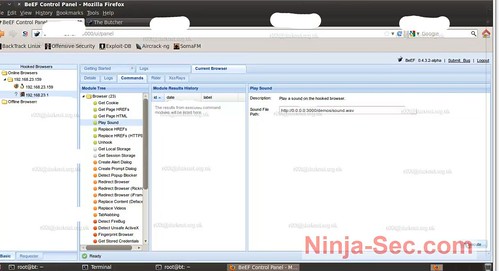
So for example if you a reasonable idea of what tools do, but aren’t really sure how, when and what to use them for exactly – this course would be very beneficial for you. For example it goes into depth into stuff on how to hone your skills on vulnerable sites like WackoPicko, plus in depth examples using Metasploit on other more niche tools like BeEF – The Browser Exploitation Framework.
The real monster of a module is 7 with 4 hours 58 minutes of video and 60 pages of slides, which is where the focus should be for me. Web Application Security is what is hot now and has been for the past couple of years, more and more web apps are being built and rolled out so it’s more likely you’ll land in a role where these skills are needed.
Labs
The labs consist of a 3-stage network with N00bs Network, Shad0w Network and Impossible Network. Each host is dual-homed so you have to attack them in sequence, you can’t for example attack Impossible Network straight from N00bs Network.
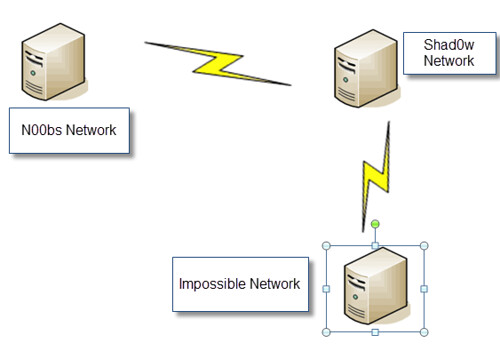
The lab is a great way to exercise some of the skills you’ve gained from following this penetration testing course and is definitely a plus point of signing up for this course.
Conclusion
This is a solid course, it’s not the most polished course I’ve ever seen – but it’s very technically competent. Some people may struggle with the heavy Arabic accent in the video material, so I’d suggest watching the samples first and make sure you’re ok with that and you can follow what Mohamed is saying.
Another thing which could be a pro or a con is the pacing, most educational videos tend to cut away when stuff is happening – which obviously makes the pace a lot faster. In CODENAME: Samurai Skills the screen-cast is in real time, which means if a tool is loading or takes a while to run (just like it does in real life) you can sit and watch it.
In a way it gives you a good insight into the reality of the pace of penetration testing (no it’s not like Swordfish) – but for some people, you may find this frustrating.
I’d say if you’re just starting out or you want to get your hands on some material that guides you step by step how to carry out attacks – this course will be valuable to you. It will take you to a place where you’ll be able to start carrying out penetration tests.
It’s not the most intense infosec/pen-testing course out there, but it does deliver a lot of value for the price and I’m looking forwards to seeing how it improves and checking out the more advanced course when it hits the market.
Other plus stuff is you get a FREE subscription to HAKIN9 Magazine when you enroll along with a full years support in the forums.
The pricing for the course & lab access is currently as follows:
- CODENAME: Samurai Skills Course Online v2 + 30 days access to Ninja-Sec Lab + NS|PT Certification = $490 USD
- CODENAME: Samurai Skills Course Online v2 + 60 days access to Ninja-Sec Lab + NS|PT Certification = $590 USD
- CODENAME: Samurai Skills Course Online v2 + 90 days access to Ninja-Sec Lab + NS|PT Certification = $690 USD
You can read more and sign up here:
