Introduction
I do examine Security Software now and then to see what’s going on, if there are any new developments and what the state of affairs is when it comes to consumer grade Antivirus and Firewall software. Countermeasures are useful, especially when it comes to less tech savvy users (which we may happen to live with/be related to/work alongside etc).
It’s been a fair few years since I’ve looked at consumer grade protection, especially since Windows 7 does a fairly good job out of the box with UAC and the basic firewall built in.
The software I’m going to be looking at is from Bitdefender Antivirus and it’s called Bitdefender Internet Security 2012 – it came out not too long ago.

It’s a neatly packaged piece of software and it’s very easy to get it up and running, it’s using a web-type installer so you will need an Internet connection and it scans whilst it’s installing – so it’s pretty efficient.

After that it pretty much runs itself, you don’t really need to touch anything out of the box – for the average user it’s configured fairly sanely by default. It’s basically a one click install.
Just make sure you don’t have any other AV software installed when you try and install it, or things could go horribly wrong (I had Avast! running on the test machine and it completely locked up – I installed it on a clean VirtualBox Win7 after that and it was fine).
Features
Feature wise it has what you’d expect, anti-virus, firewall, parental control, privacy control and anti-spam. It does have some more advanced configuration options and dialogues if you’re into that kind of thing, for example you can check out active network connections (including PID, process name etc) – which is something that always fascinated me.
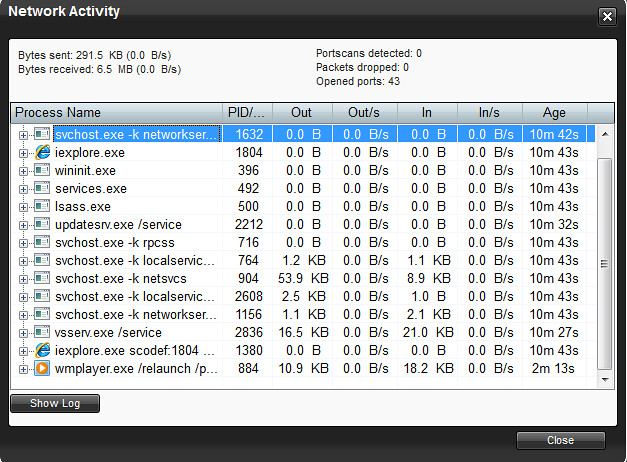
It does annoy me a little that I can’t re-size the Network Activity dialogue – but that’s a minor gripe.
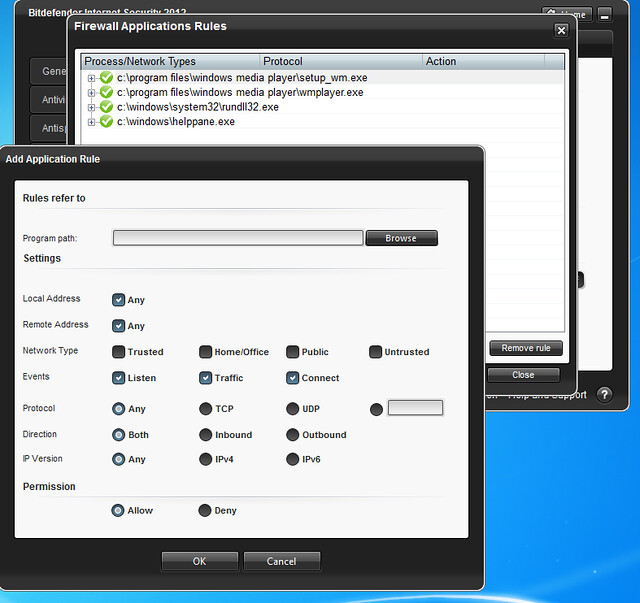
You can add fairly complex firewall rules as well, if that kind of things floats your boat. But honestly with the majority of desktop computers behind a NAT router – incoming firewall filtering has become pretty much redundant. Outgoing filtering, and more importantly alerting – is of course something which helps in the fight against malware.
There’s two things I particularly like about this software, the first appeals to my human side – which is the Autopilot mode. This makes a lot of sense and makes security a lot less intrusive (something which is really important, as the more intrusive/disruptive something is – the more likely the user is to disable it).
It updates silently, it deals with threats quietly, it just takes care of business and doesn’t get in the way.
Autopilot essentially attempts to make the optimal security-related decision when an event occurs without interrupting the user. And the setting is as simple as can be, it’s just a switch on the home screen of the application.

The other thing I love is Game Mode! It attempts to set itself automatically, but you can turn it on with a short-cut, or by using the context menu on the system tray icon.
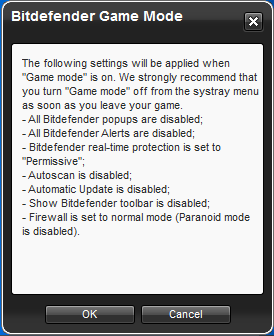
This makes a lot of sense to me – leave me to game in peace! It’s a pretty good feature if you ask me.
Other than that, Bitdefender seems fairly timely with threat updates (we have mentioned them numerous times before) as they do some pretty good research.
The most recent piece uncovered by them was pretty interesting – Super Powered Malware Sandwiches Found In The Wild – Frankenmalware.
Conclusion
In conclusion, it’s a pretty solid and unusually fuss free piece of software. You can download the trial to check it out and it’s priced pretty reasonably:
- £29.99/$49.95 for 1 PC
- £39.99/$69.95 for 3 PCs
- £69.99/$109.95 for 5 PCs
Have a play around with it, you can do so on a VirtualBox install if you don’t want to mess with your current rig. It’s a good choice to install on your non-techie friend/family-member/colleague’s computer and keep them a little bit safer.
Resource wise it seems extremely efficient, on the instance I tested the Security Center maxed out at about 7MB memory use and the agent at about 1.5MB (whilst idling). Running a Quick Scan from the home dialogue took it up to about 22MB total memory usage – which is still very impressive.
This is some pretty lean software.
If you are already using it, or are thinking of trying it out – leave your thoughts in the comment box below.
If you want to find out more or download a trial version (valid for 30 days) you can do so here:

Susann Precise says
Good day. Very cool web site!! Man .. Beautiful .. Wonderful .. I will bookmark your website and take the feeds also…I’m glad to locate numerous helpful info here within the post. Thanks for sharing…