SIPVicious SIP Scanner is a suite of tools that can be used to audit SIP based VoIP systems. Why the name? Because the tools are not exactly the nicest thing on earth next to a SIP device.
Features for SIP Hacking with SIPVicious
It currently consists of five tools:
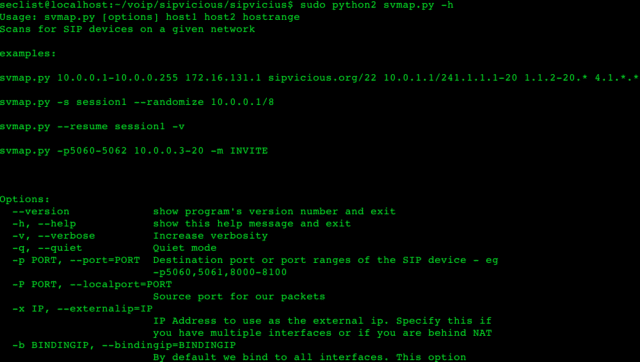
- svmap – This is a sip scanner. When launched against ranges of IP address space, it will identify any SIP servers which it finds on the way. Also has the option to scan hosts on ranges of ports.
- svwar – Identifies working extension lines on a PBX. A working extension is one that can be registered. Also tells you if the extension line requires authentication or not.
- svcrack – A password cracker making use of digest authentication. It is able to crack passwords on both registrar servers and proxy servers. Current cracking modes are either numeric ranges or words from dictionary files.
- svreport – Able to manage sessions created by the rest of the tools and export to pdf, xml, csv and plain text.
- svcrash – Responds to svwar and svcrack SIP messages with a message that causes old versions to crash.
Requirements for SIPVicious
Python is the main requirement, it should work on any system that supports Python 2.6 or greater.
It was tested on the following systems:
- Linux
- Mac OS X
- Windows
- FreeBSD 6.2
- Jailbroken iPhone with python installed
There is also:
– ohrwurm – RTP Fuzzing Tool (SIP Phones)
– SIPcrack – SIP Login Dumper & Hash/Password Cracker
– Sipflanker – Locate SIP (VoIP) Device Web Interfaces
– SIP Proxy – VoIP Security Testing Tool
– Mr.SIP – SIP Attack And Audit Tool
You can download SIPVicious here:
Or read more here.

Rafael Santana de Sousa says
Hey, thank you for this site.
Can I ask you something? A have a site that blocks ‘_’. I found a SQL Injection there. It’s a MySQL 5.1 nut I not able to exploit this because of this damn filter. So i can’t run SELECT schema_name FROM information_schema.schemata; or SELECT table_schema,table_name FROM information_schema.tables WHERE table_schema != ‘mysql’ AND table_schema != ‘information_schema’, etc.
Do you know any way to bypass this filter?
Thank you