MoocherHunter is a mobile tracking software tool for the real-time on-the-fly geo-location of wireless moochers and hackers. It’s included as part of the OSWA Assistant LiveCD we mentioned quite recently.
What does MoocherHunter do?
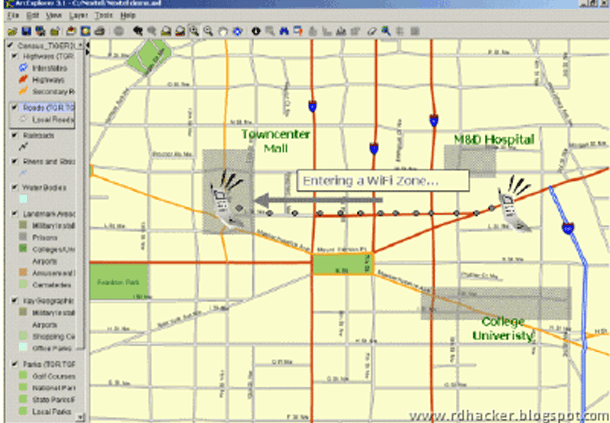
MoocherHunter identifies the location of an 802.11-based wireless moocher or hacker by the traffic they send across the network. If they want to mooch from you or use your wireless network for illegal purposes (e.g. warez downloading or illegal file sharing), then they have no choice but to reveal themselves by sending traffic across in order to accomplish their objectives.
It enables the owner of the wireless network to detect traffic from this unauthorized wireless client (using either Passive or Active mode) and enables the owner, armed with a laptop and directional antenna, to isolate and track down the source.
Because it is not based on fixed or statically-positioned hardware, MoocherHunter allows the user to move freely and walk towards the actual geographical location of the moocher/hacker. In residential and commercial multi-tenant building field trials held in Singapore in March 2008, Moocher Hunter allowed a single trained operator to geo-locate a wireless moocher with a geographical positional accuracy of as little as 2 meters within an average of 30 minutes.
Download MoocherHunter
You can download OSWA Assistant here to get MoocherHunter:
Or read more here.

d347hm4n says
Very interesting, shame the tool isn’t in BT. Maybe it will be in the next release.
geek.4.fun says
it would be a nice addition to BT, you could always just add it yourself in the mean time, I did. :)
d347hm4n says
Yep, I think I will have to do that >.>
zupakomputer says
I’d have to mooch someone’s wireless anyway to even consider being able to download a file that size.
Suburbia says
Cool tool, but if you’re trying to track down mooches, doesn’t that mean A. Your network is open or B. You’ve used an inferior method of encryption to secure your network?
elpeor says
I spoke with that software developers and they will not open source the application, they just give for free with that live CD and only in that live CD.
Anybody knows any other application similar to that on? The live cd did not work well in my little pc an I want something similar for my gentoo box.
thanks..
localhost says
geek.4.fun & d347hm4n becareful and look at license befour run the moocherhunter softwares outside of oswa assistant, it says it only license for use in oswa assistant, think it not be foudn anyware else on other cd unless the other peeple want get sued.
gul says
OMG ! This topic went really far from it’s original subject :p
So, that moocher hunter is just part of a liveCD, not in the open source community… sad. Anyway, I’ll do like you folks, wait for my bandwith to allow me to get it, and try it at home :)
Plus I have to do more testing in nUbuntu… Will be fun… Gonna miss some nights ;)