[ad]
Competition time again!
As you know we started the Darknet Commenter of the Month Competition on June 1st 2007 and it’s been running since then! We have just finished the eleventh month of the competition in April and are now in the twelfth, starting a few days ago on May 1st – Sponsored by GFI.
We are offering some pretty cool prizes like iPods and PSPs (or similar), along with cool GFI merchandise like shirts, keyrings and mugs.
And now the winner will also get a copy of the Ethical Hacker Kit.

Keep up the great comments and high quality interaction, we really enjoy reading your discussions and feedback.
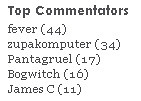
Just to remind you of the added perks, by being one of the top 5 commenter’s you also have your name and chosen link displayed on the sidebar of every page of Darknet, with a high PR5 (close to 6) on most pages (4000+ spidered by Google).
So announcing the winner for April…it’s fever! He had a 10 comment lead on zupakcomputer, fever another new-comer came out of nowhere.
Comments for May have been very low so far, so it might be an easy win for someone this month :)
April saw some good discussions and was a little more lively than March, I hope May picks up bit! I’d like to thank you all for your participation! I hope it keeps getting better as 2008 develops with more interesting news and tools. Keep up the excellent discussions, it’s very interesting reading especially on some of the more controversial topics.
Thanks to everyone else who commented and thanks for your links and mentions around the blogosphere!
Feel free to share Darknet with everyone you know :)
Keep commenting guys, and stand to win a prize for the month of May!
We are still waiting for pictures from backbone, Sandeep and TRDQ, dirty and dre, eM3rC, fever, Sir Henry and goodpeople of themselves with their prizes!
Winner for June 2007 was Daniel with 35 comments.
Winner for July 2007 was backbone with 46 comments.
Winner for August 2007 was TheRealDonQuixote with 53 comments.
Winner for September 2007 was Sandeep Nain with 32 comments.
Winner for October 2007 was dre with 19 comments.
Winner for November 2007 was dirty with 38 comments.
Winner for December 2007 was Sir Henry with 84 comments.
Winner for January 2008 was goodpeople with 66 comments.
Winner for February 2008 was eM3rC with 122 comments.
Winner for March 2008 was Pantagruel with 66 comments.

zupakomputer says
hee-hee, eM3rC gave you a fake e-mail? You should really expect that kind of thing, being a hacking site. I mean, how does anyone know you’re not just spying on all potential subversives.
I just like to state out loud what everyone else thinks but won’t say cause they think they’ll make more money if they keep quiet. Who cares? Who’s going to do anything if you do say / write it out loud? Everyone doing it for a living are still going to get plenty of business from all the dum-dums that don’t have a clue on how their networks work; I’ll be more likely to get hired after typing that.
Bogwitch says
Well done fever. Good luck with the job hunt zupak!
Changlinn says
I am too much of a wuss and feel unworthy to comment usually. You guys put together some damned good articles though. Maybe make a wiki of the tools rather than having us have to search back through the posts.
fever says
thank to all of you who commented. if no one else had made comments than it would have been a boring discussion. it was very interesting and you all have some good insight. thanks again. keep the comments coming. long live the community.
why isnt there a second place prize too? i think it i well deserved.
macdaddy says
yeah, this site seems like they have a lot of work everyday. Seeing that they put up a post almost daily.. Great work fever : ) and the Darknet team.
eM3rC says
Hey everyone,
Thought I’d make a comeback at the beginning of a new month. Reason for being gone so long is a shit ton of testing, finals, work applications, college stuff and relationship drama ;P
@ zupakomputer
I didn’t use a fake email. Just one of my slave ones. I have a few emails set aside. The first one for personal stuff, second for spam stuff, and the last one for everything hacking related. I dont check the spam and hacking ones regularly so that’s why I didn’t respond quickly to Darknet’s emails. Also had problems with my cell (which is my home phone) so calls also were a problem. Hopefully that’s all worked out now.
Gratz fever on winning the competition!
Looking forward to posting again and good luck to those of you who should win but haven’t yet (you know who you are).
Sarah says
Hey fever! a BIG well done from all of us at GFI. Your prizes are on the way so look out for them in the post within a few days. Congrats to all the runners-up as well. Keep on commenting… you might be the next winner next month :)
Pantagruel says
Congrats, well done.
Been a slow month for me due to my ‘real’ work (researcher by nature), will get some commenting done this month (hopefully)
macdaddy says
i hope to do some good commenting :P
Darknet says
eM3rC gave a real e-mail, hes gotten the prizes now.
Changlinn yah it’s about time we did some more summary/list articles. Rather busy at the moment though.
We do try and rock an article every weekday, and take a break at the weekends :D
Keep on commenting guys, we thrive on your comments…it’s validation that something is cool or interesting if it sparks a decent debate.
zupakomputer says
Oh, I forgot to say congrats to fever!
So – congrats to you fever.
Fever says
thanks zupak
Howard says
Wow! It is amazing to see a tremendous amount of people dedicated to the fine art if intelligent hacking (with ethics).One of the most exiting sites seen through my eyes.I am a 53 year old newbie to this but having the time of my life.Wish I knew all these people earlier in life could have had fun….I am having a few problems understanding but am catching on by listening to the pro’s.I do not know Fever but good showing my friend smart cookie…..I will keep reading so keep writing
hats off to all As the crowd cheers all of the pro’s and writers and commenters take their bow……. champions i a world that is confused about life
HC
Jinesh Doshi says
Congratulations to the winner.