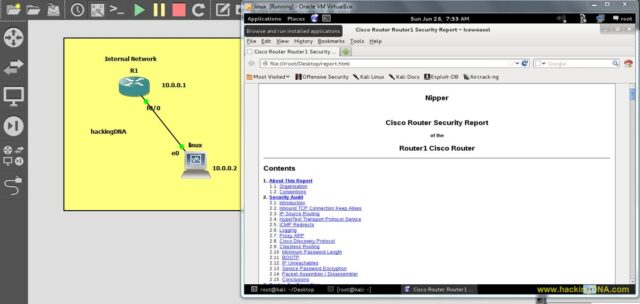
Get your Nipper tools download here, this tool performs security audits of network device configuration files. The report produced by Nipper includes; detailed security-related issues with recommendations, a configuration report and various appendices.
Nipper has a large number of configuration options which are described in the lists below.
Devices Supported by Nipper Tools
Nipper currently supports the following device types:
- Cisco Switches (IOS)
- Cisco Routers (IOS)
- Cisco Firewalls (PIX, ASA, FWSM)
- Cisco Catalysts (NMP, CatOS, IOS)
- Cisco Content Service Switches (CSS)
- Juniper NetScreen Firewalls (ScreenOS)
- CheckPoint Firewall-1 (FW1)
- Nokia IP Firewalls (FW1)
- Nortel Passport Devices
- SonicWALL SonicOS Firewalls (SonicOS)
The security audit includes details of the findings, together with detailed recommendations. The security audit can be modified using command line parameters or an external configuration file.
Further Nipper Tools Features
Network filtering audits include the following, all of which can be modified:
- Rule lists end with a deny all and log
- Rules allowing access from any source
- Rules allowing access from network sources
- Rules allowing access from any source port
- Rules allowing access to any destination
- Rules allowing access to destination networks
- Rules allowing access to any destination service
- Rules that do not log
- Deny rules that do not log
- Rules that are disabled
- Rules that reject rather than drop
- No bypass rules exist
- Default rules
This update (0.11.5) includes improvements to support for Cisco PIX / ASA / FWSM firewalls, SonicWALL SonicOS firewalls, CheckPoint Firewall-1 and Nokia IP firewalls. It also includes a host of other updates.
The output from Nipper can be in HTML, Latex, XML or Text formats. Furthermore, Nipper will reverse any Cisco type-7 passwords identified, all other encrypted passwords can be output to a John-the-Ripper file for further strength testing. By default, input is retrieved from stdin and is output (in HTML format) to stdout.
Nipper is available for Linux, Windows and other platforms. You can download Nipper Tools here:
Or read more here.
