Unicornscan is a new information gathering and correlation engine built for and by members of the security research and testing communities. It was designed to provide an engine that is Scalable, Accurate, Flexible, and Efficient. It is released for the community to use under the terms of the GPL license.
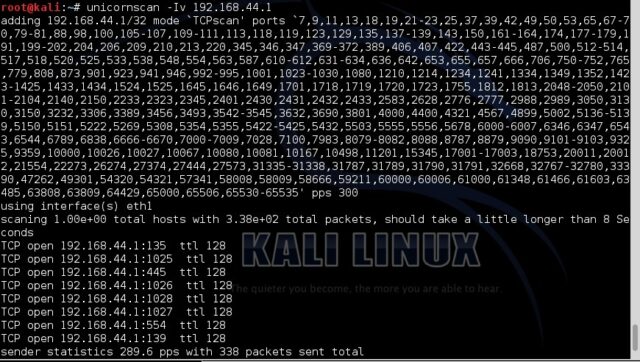
It has always been a favourite of mine, especially for UDP scanning and scanning large networks (and getting it done fast).
In some ways the implementation is better than Nmap – in some ways worse. Both are great tools and for me, they work well hand in hand, both have certain advantages over the other in different situations.
I did get halfway to writing an article about Nmap vs Unicornscan for large network scanning.
Benefits of Unicornscan
It is an attempt at a User-land Distributed TCP/IP stack. It is intended to provide a researcher with a superior interface for introducing a stimulus into and measuring a response from a TCP/IP enabled device or network. Although it currently has hundreds of individual features, a main set of abilities include:
- Asynchronous stateless TCP scanning with all variations of TCP Flags.
- Asynchronous stateless TCP banner grabbing
- Asynchronous protocol-specific UDP Scanning (sending enough of a signature to elicit a response).
- Active and Passive remote OS, application, and component identification by analyzing responses.
- PCAP file logging and filtering
- Relational database output
- Custom module support
- Customized data-set views
Anyway, the good news is it has finally been updated and v0.4.7 is available and released for download.
Your Unicornscan download of the fast port scanner is here:
Source Code: unicornscan-0.4.7-2.tar.bz2

Sir Henry says
I have spent the last hour working on getting the source installed. Unfortunately, configure is looking for something that apparently cannot be found:
checking for PostgreSQL… configure: error: cant find PostgreSQL header libpq-fe.h
I have to wonder if it is due to the fact that I went the lazy way and just did apt-get install for PostgreSQL. Until I get this figured out, I will not be able to provide my initial thoughts. meh.
Robert E. Lee says
If you install the postgres-devel package, Unicornscan’s configure should be able to find libpq-fe.h. That should only be required if you’re using –with-pgsql in the configure. If you drop the –with-pgsql, you can compile unicornscan without database output support.
–Robert
lars says
apt-get install libpcap0.8 libpcap0.8-dev flex-old bison libnet1 libnet1-dev
That did it for me after an Etch minimal setup.
Unicornscan wants to install to /usr/local/libexec/ by default – just create the dir if you’re lazy and you should be done ;)
goodpeople says
I’m currently in the process of rebuilding my network at home, so unfortunately I don’t have a spare Linux box to test this on.
I was wondering about Sir Henry’s pgsql tho.. Why the pgsql and not mysql by default…
Sir Henry says
@goodpeople:
I am still having library issues with getting this set up, even without the postgres flag being removed from configure. I did try with MySQL (since it does reference that you are not using it in the configure results), but got a similar devel error as with postgres. Due to other items of higher priority (ramping up for my new job), I have let it lie for now.
goodpeople says
@Sir Henry,
Can’t you use RPM’s with Ubuntu?
Sir Henry says
Yes, I can, but I wish to exhaust myself with trying to get it to work from source. That is how I have always been. Given, it has helped me learn a lot, but I am certain that I have lost a lot of hair and time over it.
goodpeople says
@Sir Henry,
Ah, nice, another hardliner.. :-)
eM3rC says
Wow! Looks like a great program. I have been using nmap for quite some time and now it seems like theres something out there that is even better. Thanks darknet!