The MSF eXploit Builder (MSF-XB) is a free win32 application (GUI) that wants to be an Exploit Development Platform. The main goal is to speed up the exploit development process, this is accomplished by using the powerful functionalities and neat design of The Metasploit Framework.
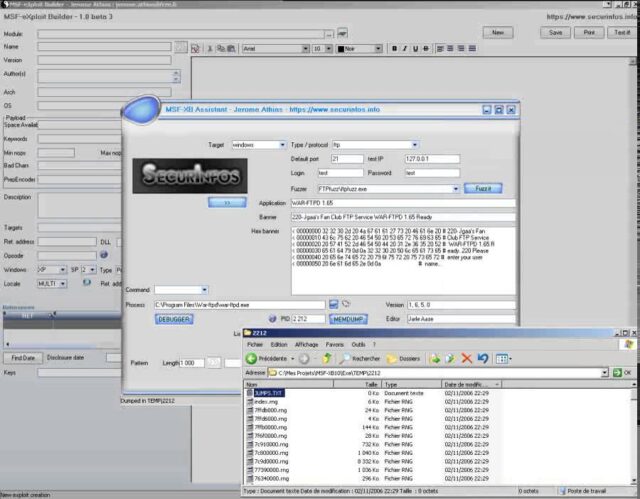
MSF-XB automatically generates MSF compliants exploits modules.
What is an Exploit
An exploit (from the English verb to exploit, meaning “to use something to one’s own advantage”) is a piece of software, a chunk of data, or a sequence of commands that takes advantage of a bug or vulnerability to cause unintended or unanticipated behavior to occur on computer software, hardware, or something electronic (usually computerized). Such behavior frequently includes things like gaining control of a computer system, allowing privilege escalation, or a denial-of-service (DoS or related DDoS) attack.
From: Wiki
MSF Exploit Builder Development Platform
The MSF-XB package also includes for your convenience:
Fuzzers
- TAOF, The Art Of Fuzzing v0.3.2
- ProxyFuzz v0.1, Rodrigo Marcos
- FileFuzz v1.0.2510.28439, iDefense
- FTPfuzz v1.0, Infigo
- WinFuzz v1.0.0.1, Fakehalo
Handy Tools
- Findjmp2, Class101
- branchseeker
- Faultmon
- mycrc
- Sysinternals (Microsoft) PStools
- wget.exe, GNU
- xCmd (remotexec clone)
- nc.exe
- A local database of opcodes/return addresses (Cross-platforms, 10 locales, fast and reverse queries)
- An ASCII table
- A lot of converters (Ascii, Hex, Byte, Unicode …)
- Malcode Analyst Pack v0.2
- Process Stalker, iDefense
MSF Exploit Builder Requirements
- Please edit and customize the MSF-XB.INI file
- MSF-XB requires the Metasploit Framework installed to work properly (http://www.metasploit.com ): Version 3 is recommended
- MSF-XB requires a debugger to be installed (Immunity Debugger)
You can download MSF eXploit Builder here:
MSF-XB.EXE (No longer Available) (84Mb)
MD5 41e83b8cb8d60d689bff191eb7842fc1
SHA1 1cb0e457c9fa59da8f147a96afb9c1a056a4e655

Goodpeople says
I’ll leave the exploit building to the people that are good at it. I’m not a researcher. I teach security specialists.
James says
This is going to save me so much time.
CG says
its a good tool and Jerome put alot of work into it. there is also a video and paper on how to use it on his site, very good stuff
net2004eng says
This is way cool!!!
This is perfect for people not only attempting to learn what the bundled exploits in MSF do, but also – of course – for those people who are actively developing exploits. Another major piece to this is that it is a Windows based tool as well…
Hats off to the developers!
Pantagruel says
After toying with MetaSploit, this is definitely going to get tested. I just can’t help it, curious by nature. Furthermore it will come in handy for all my Windows bound colleagues who still thing my penguin to be a fluffy toy.
Sir Henry says
I agree with Pantagruel. The curiosity here is paramount and intoxicating. Although I am not someone who normally looks to craft exploits (not for lack of want), but this is something with which I shall have to experiment. I just need to get Windows on a system somewhere.
fak3r says
This is hilarious, I need to see if it’ll run under Wine! If not I may slap VirtualBox on Linux to play with this. What’s next, an Eclipse plugin for Metasploit? Too fun!