[ad]
After almost a year of intensive development and internal use, Immunity (The guys who bought us CANVAS) has announced the public release of Immunity Debugger v1.0. The main objective for this tool was to combine the best of commandline based and GUI based debuggers.
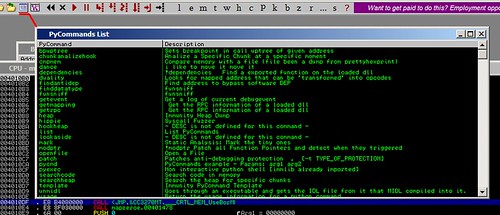
Immunity Debugger is a powerful new way to write exploits, analyze malware, and reverse engineer binary files. It builds on a solid user interface with function graphing, the industry’s first heap analysis tool built specifically for heap creation, and a large and well supported Python API for easy extensibility.
- A debugger with functionality designed specifically for the security industry
- Cuts exploit development time by 50%
- Simple, understandable interfaces
- Robust and powerful scripting language for automating intelligent debugging
- Lightweight and fast debugging to prevent corruption during complex analysis
- Connectivity to fuzzers and exploit development tools
Immunity Debugger’s interfaces include the GUI and a command line. The command line is always available at the bottom of the GUI. It allows the user to type shortcuts as if they were in a typical text-based debugger, such as WinDBG or GDB. Immunity has implemented aliases to ensure that your WinDBG users do not have to be retrained and will get the full productivity boost that comes from the best debugger interface on the market.
Basically they’ve ended up creating a fully flexible and extensible Win32 debugger that has all of it’s features, both debugging and graphical, easily accessible from it’s Python scripting engine.
And best of all, it’s available for free. That’s right, Immunity Debugger is released for free, including free monthly updates.
You can download Immunity Debugger here, after registration.
http://debugger.immunityinc.com/register.html
Yes this goes against our general policy of not including tools that require registration, but this one is too cool to miss, so grab it! This is seriously cool and could well replace Ollydbg as the hackers choice. Along with IDA Pro and SoftIce of course ;)
Or read more here.

backbone says
great tool… but for guys like me there can be only two debuggers: SoftIce and GDB. Because I am not a exploit developer :
malfunction says
actually it’s ollydbg. they only licensed the engine and added this python scripting and graphing stuff. see http://www.woodmann.com/forum/showthread.php?t=10343 for further diskussion. and for softice, i think it has had it’s time.. to cumbersome to get it working. apart from iceext i know nothing which would keep me from using syser all the time. ida pro, well debugger isn’t as nice as the disassmbler but still good enough for a quick trace.
TheRealDonQuixote says
@Malfunction – Nice work there. Do you think the added python scripting and graphing makes Immunity Debugger any better than ollydbg? What about the claims that exploit time is cut in half? Also, I have discovered that Immunity debugger doesn’t run so well in WINE, actually not at all really. Still, what do you think about the supposed speed increase?
BTW – Link for syser plz? I’ve never used it.
malfunction says
first of all sry for my late follow up. at the moment there is not much difference betwenn olly and immunity. olly can be easily extended via plugins. there may be no python plugin but you can get perl scripting for sure :P for the graphing, i far as i can remember the lib from ida pro is freeware. but i’ve never used this feature in ida, it confuses me more than it helps. concerning the speedup i would say it’s mainly markting speech. it only boils down to the scripting capabilities and you can have that in ida (python plug) and olly too. here’s the syser link, if you haven’t googled it already: http://www.sysersoft.com/download/download.php
TheRealDonQuixote says
@Malfunction
Actually its good you wrote back. Better late than never. I had completely forgot about syser.
Thanks for the link!
ROke says
Goood very goood!
bogsheet says
if this is a great tool it’s only coz it’s olly!
so i would say in fact olly is a great tool, and these guys are complete chancers. they have ripped off oleh yushuk’s amazing work in creating ollydbg and are passing it off as their own! it certainly looks that way.
let’s be honest, they could have just released a python plugin for olly (that’s all this is) without reskinning it and making it look like they should be credited with the entire debugger. plus it would be much better and easier for people to just add the plugin to their olly rather than using a second skinned instance of olly instead.
boo – poor form, these guys are losers!
goober says
Uhhhm bogsheet they licensed ollydbg – might want to pay closer attention