Odysseus is a proxy server, which acts as a man-in-the-middle during an HTTP session. A typical HTTP proxy will relay packets to and from a client browser and a web server. Odysseus will intercept an HTTP session’s data in either direction and give the user the ability to alter the data before transmission.
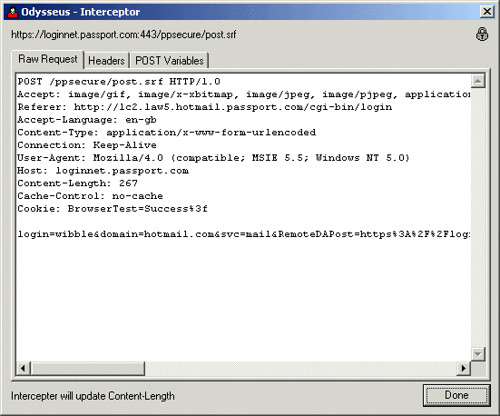
For example, during a normal HTTP SSL connection a typical proxy will relay the session between the server and the client and allow the two end nodes to negotiate SSL. In contrast, when in intercept mode, Odysseus will pretend to be the server and negotiate two SSL sessions, one with the client browser and another with the web server.
As data is transmitted between the two nodes, Odysseus decrypts the data and gives the user the ability to alter and/or log the data in clear text before transmission.
Features
- Multi-threaded native Win32 executable – The use of native Window code, combined with extensive multi-threading, means that Odysseus is fast. Speed was a primary development objective.
- No external dependencies – Everything needed to intercept web requests (apart from a browser configured to use Odysseus as a proxy :) is included in the distribution archive. No additional downloads or installations are required.
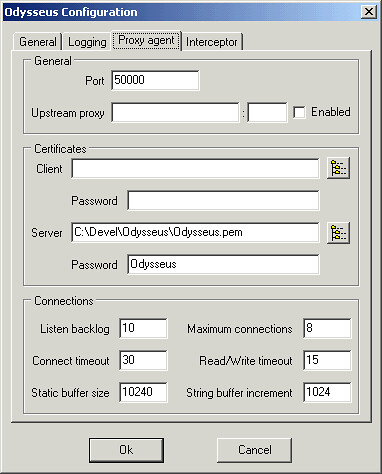
- Flexible & configurable – A wealth of configuration options means Odysseus should be flexible enough to meet the needs of nearly any web based application assessment.
- Low desktop profile – Odysseus doesn’t clutter your desktop with redundant windows. A simple System Tray icon is all that is needed to access it’s many features. The various components of Odysseus appear and disappear as configured, or instructed, by the user.