[ad]
I saw some interesting information recently on a mailing list.
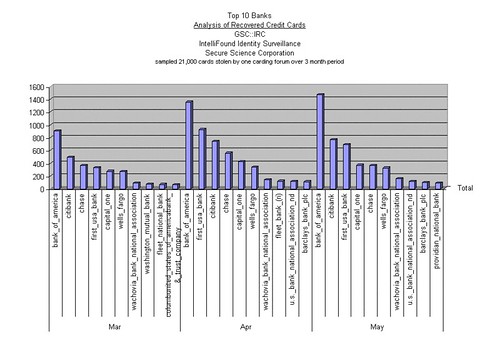
We took one sample of one carding/phishing forum that our Global Surveillance Center was monitoring and sampled the set into a graph that lists the top 10 banks and the losses over the last month. As you can see, it’s obvious who the top credit card companies are out there, but at the same time, we can see an ever increasing on the top targets but not necessarily an increase on the lower tiers over the entire three months, but in the first two we see a significant increase in success with stolen credit cards in general. In this case, the loss that we captured (which probably isn’t nearly the number captured by this forum) was a little over 21,000 credit cards.
This is one group, with 21,000 cards per 3 months (that we know about) and law enforcement estimates about $500.00 per card in average loss. At that rate, in 3 months, one carding group causes $10,500,000.00 in loss. And this carding group is at the low end of the totem poll.
As you can see from the graph, Bank of America is highest on all counts, perhaps they need to think about addressing that? First USA bank and Citibank make up the other 2 of the top 3.
Credit:
Lance James
Secure Science Corporation
http://www.securescience.net

steve b says
very interesting read, graph is very telling too