[ad]
Well seen as though I tell the others to do some kind of introduction, probably I should do one for myself too.
Then
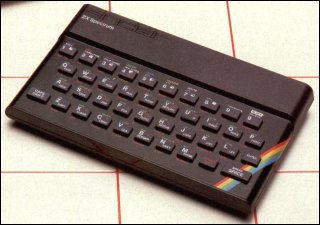
I started out with a Spectrum ZX-81 back in the olden days, typing whole games out of the Spectrum magazines I picked up from charity shops.

Yah it had no tape drive, no disk drive, no hard drive..nothing. Once you powered it off, you lost everything. I missed the ugly white ZX-80 just by a few months.
It was a powerful beast.
- Z80A Microprocessor clocked at 3.25MHz.
- 1K RAM, expandable to 16K, 32K or 56K.
- 8K ROM containing BASIC.
- A single ULA for all I/O functions.
After that I quickly upgraded to a Spectrum 48K +, which was a little better and had an external tape deck.
This was where I learnt the basics of computers and programming..my friends had a mixture of things Commodore 64’s and Amigas for the rich kids with the odd Atari here and there.
After that was a Spectrum 128k + with an integrated tape drive.
Back in those days pirating games consisted of a hi-fi with tape-tape capability and a blank tape (plus half an hour of listening to some weird screechin noises).
At secondary school I learnt a bit more with some BBC Basic and a little DR-DOS on the RM Nimbus’s, I remember the beast of the school was a 486-DX66 with a 40mb hard drive or something like that.
I used to hack the network back then to try and play games like PGA Golf, Budokan and Lesuire Suit Larry!
After that I couldn’t afford a PC at home, so I went onto consoles, as that was all I could afford at the time (NES, SNES then PSX).
I kind of drifted away from computers until I had finished college and got back into them during my failed first year of a Electrical and Electronics Degree, I quickly shifted to Software Engineering..during my first year I got all my downloaded warez deleted because I had shared NetBIOS over TCP/IP so some random NBT scanner on the internet had deleted all my stuff.
After that I started learning about networking, security, file permissions and it went on from there.
A year or so later I founded Darknet with another friend on IRC network DALnet and around 1998 I setup this domain.
You can see the old page as it was 5 years ago HERE. There are no earlier versions (thankfully). Yah I know it doesn’t work in Firefox, embarassing eh?
Now it’s about 8 years later, and I know a fair bit about computer security.
Now.
I am now working in information security, my main role being a lead of the attack and penetration team. I also do various other things such as disaster recovery, digital forensics, security audits in compliance with various standards (including BS7799), on the side I do web design (like this site) and various other hobby sites.
My main job though is penetration testing/vulnerability assessment and keeping up with all the latest technologies. I am especially good in information gathering (what the media has labelled as Google Hacking).
After that my strongest suite is the network stack, I’m good down to the packet/header level, not so great at programming, but I can script do PERL/PHP/Bash etc.
I got a lot of experience doing system administation jobs and self-studying in a lab at home, also learnt a lot about Linux in a previous job doing a transition from Windows servers to Linux servers, all from my recommendations.
In my spare time I write about security, I read books, I hack PHP, I enjoy food and the countryside.
I have a few industry certifications, but I don’t really place much emphasis on them, so I won’t really be talking about those. Practical hands on experience is the best you can do.
Future?
I’m a general knowledge kind of guy, and my skills are in info gathering so a lot of my input is news articles and current trends/discussion. I also plan to write many articles about the various aspects and parts of penetration testing as started with my Rainbow Tables/Rainbow Cracking article and my discussion on Social Engineering in Penetration Testing.
Being in the business, I am up to date with the latest tools/exploits/developments so I’ll try and share that all with you.
If you have any questions, you can always contact the team.

ds says
shaolin from liverpool?
Darknet says
ds: Yah that’d be me ;)
backbone says
well the mistery man revealed… :)
so everybody started with games…
Navaho Gunleg says
True — if some guy didn’t think of the idea to create computer-games I think a lot of people (read: ‘the mainstream’) wouldn’t have touched those things in the 80s, or even 90s.
Luckily, some guys saw they could make the big bucks creating games for these home-computers.
Sadly, I wasn’t one of those guys. :)
Navaho Gunleg says
Oh btw, you say
That old page looks OK here, though?
Darknet says
Yeah thank the lord for games :)
Navaho: Try scrolling the middle panel in Firefox or any browser that’s not IE (You can’t, the scroller isn’t there) ;) Then try it in IE it works fine. (Loads faster locally here)
Haydies says
Not every one started with games, but I have to say I like the advanced zx81, least that one had keys… I personaly think if your going to be hard core, you need a z80, now thats where its at for true power :-)
More seriously, its games that have pushed computer technology for ever, always has, always will… business apps just don’t need all that much.
Ralph Corderoy says
It’s a Sinclair ZX81, not a Spectrum ZX81. And you were probably typing in stuff from Sinclair magazines, not Spectrum ones, like Sinclair User, Sinclair Programs. Also mags like Your Computer would have listings for various machines.
Cheers,
Ralph, who also started with a ZX81.
Darknet says
Ralph: Ah yah you would of course be right..silly me, it was so long ago. Sinclair ZX81 indeed, who can forget Mr. Sinclair and his C-5 :) Yeah those magazines sound familiar too, was probably them!
Ubourgeek says
Heh! The ZX81 photo brought back memories – A Timex Sinclair was the first ‘puter I over owned (my friend gave it to me when his ‘rents bought hime a TI994A) and programmed on.
In my antique computer collection, I’m lucky enough to have a functional ZX81 with the 64K memory pack, thermal printer, cassette interface and a whack of tapes with various programs.
As a joke, in my library at work, I have a copy of “The Sinclair ZX81 – Programming for Real Applications” in full view on the end of the shelf along with my “modern” tomes. Thus far, only two people in the shoppe have gotten the joke – both follow “old school” geeks.
Cheers,
U.
Navaho Gunleg says
I grew up with a C64, a buddy of mine had a Sinclair. I never could get used to using shortcuts in stead of typing in the actual BASIC statement, but was amazed that that little sucker could actually do pretty nice graphics. For that time, of course. ;)
Us old-school guys grew up with, what, 8 colour graphic modes? Hell, remember playing GATO on a PC with a CGA display, with only 4 and purple sea-water?
And these spoiled kids nowadays have Nvidia graphics cards that can render movies like Tron in real-time.
Nice thing is that these same kids get crap graphics on their cell-phone. That’s something their kids will never know about. By then the ‘command line’ will be long-forgotten by the main-stream, too…
Steve says
ZX81 = Old School! I enjoy reading your posts. Keep up the great work.
_Steve
ken says
the 81 could use a tape recorder, just the same as you could on a spectrum. Are you sure you had one? You seem oddly confused about their capabilities, as though you were just writing second hand info.
Hernan says
z81,c64,atari could used TV-output. I can only reference those amazing computers. I saw a 64, touch an atari and be presented to a z81 which had lost its output capabilities.
I was amazing about PC couldn’t TV-out wiyhout an expensive added card, anything I was needing then to operate my first software for a TV ring.