Github search is quite a powerful and useful feature and can be used to search for sensitive data in repositories, this Github security scanning tool comes with a collection of Github dorks that can reveal sensitive personal and/or other proprietary organisational information such as private keys, credentials, authentication tokens and so on. github-dork.py is a […]
Python
scanless – A Public Port Scan Scraper
scanless is a Python-based command-line utility that functions as a public port scan scraper, it can use websites that can perform port scans on your behalf. This is useful for early stages of penetration tests when you’d like to run a port scan on a host without having it originate from your IP address. Public […]
PwnBin – Python Pastebin Search Tool
PwnBin is a webcrawler or Pastebin search tool which searches public pastebins for specified keywords. All pastes are then returned after sending completion signal CTRL+C. Apart from being a great tool for developers, Pastebins are often used by hackers to leak stolen credentials or d0x people. This tool can help you search pastebins for your […]
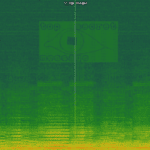
spectrology – Basic Audio Steganography Tool
spectrology is a Python-based audio steganography tool that can convert images to audio files with a corresponding spectrogram encoding, this allows you to hide hidden messages via images inside audio files. Using this tool you can select range of frequencies to be used and all popular image codecs are supported. Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 |
usage: spectrology.py [-h] [-o OUTPUT] [-b BOTTOM] [-t TOP] [-p PIXELS] [-s SAMPLING] INPUT positional arguments: INPUT Name of the image to be converted. optional arguments: -h, --help show this help message and exit -o OUTPUT, --output OUTPUT Name of the output wav file. Default value: out.wav). -b BOTTOM, --bottom BOTTOM Bottom frequency range. Default value: 200. -t TOP, --top TOP Top frequency range. Default value: 20000. -p PIXELS, --pixels PIXELS Pixels per second. Default value: 30. -s SAMPLING, --sampling SAMPLING Sampling rate. Default value: 44100. |
Example
|
1 |
python spectrology.py test.bmp -b 13000 -t 19000 |
You […]
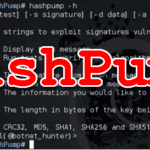
HashPump – Exploit Hash Length Extension Attack
HashPump is a C++ based command line tool to exploit the Hash Length Extension Attack with various hash types supported, including MD4, MD5, SHA1, SHA256, and SHA512. There’s a good write-up of how to use this in practical terms here: Plaid CTF 2014: mtpox Usage
|
1 2 3 4 5 6 7 8 9 10 11 |
$ hashpump -h HashPump [-h help] [-t test] [-s signature] [-d data] [-a additional] [-k keylength] HashPump generates strings to exploit signatures vulnerable to the Hash Length Extension Attack. -h --help Display this message. -t --test Run tests to verify each algorithm is operating properly. -s --signature The signature from known message. -d --data The data from the known message. -a --additional The information you would like to add to the known message. -k --keylength The length in bytes of the key being used to sign the original message with. Version 1.2.0 with CRC32, MD5, SHA1, SHA256 and SHA512 support. <Developed by bwall(@botnet_hunter)> |
You can download HashPump here:
|
1 2 3 4 5 |
$ git clone https://github.com/bwall/HashPump.git $ apt-get install g++ libssl-dev $ cd HashPump $ make $ make install |
Or read more […]