SessionGopher is a PowerShell Session Extraction tool that uses WMI to extract saved session information for remote access tools such as WinSCP, PuTTY, SuperPuTTY, FileZilla, and Microsoft Remote Desktop.
The tool can find and decrypt saved session information for remote access tools. It has WMI functionality built in so it can be run remotely, its best use case is to identify systems that may connect to Unix systems, jump boxes, or point-of-sale terminals.
How it Works
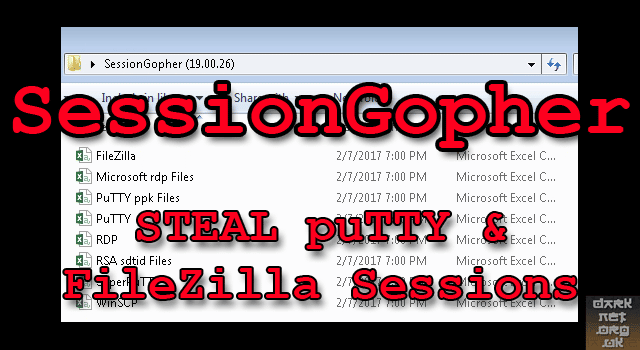
SessionGopher works by querying the HKEY_USERS hive for all users who have logged onto a domain-joined box at some point. It extracts PuTTY, WinSCP, SuperPuTTY, FileZilla, and RDP saved session information. It automatically extracts and decrypts WinSCP, FileZilla, and SuperPuTTY saved passwords.
When run in Thorough mode, it also searches all drives for PuTTY private key files (.ppk) and extracts all relevant private key information, including the key itself, as well as for Remote Desktop (.rdp) and RSA (.sdtid) files.
Usage
|
1 2 3 4 5 6 7 8 |
. .\SessionGopher.ps1 Invoke-SessionGopher -option -Thorough: searches all drives for PuTTY private key (.ppk), Remote Desktop Connection (.rdp), and RSA (.sdtid) files. -o: outputs the data to a folder of .csv files -iL: provide a file with a list of hosts to run SessionGopher against, each host separated by a newline. Provide the path to the file after -iL. -AllDomain: SessionGopher will query Active Directory for all domain-joined systems and run against all of them. -Target: a specific host you want to target. Provide the target host after -Target. |
You can download SessionGopher here:
Or read more here.
