So this is a pretty interesting acoustic based cryptanalysis side-channel attack which can crack 4096-bit RSA encryption. It’s been a while since we’ve seen anything hardware based, and RSA 4096 is pretty strong encryption, I wonder how they figured this one out.
It makes sense though when you think about it, although I wouldn’t have thought about it – I wasn’t even aware that processors made any audible noise when processing (even if the noise can only be picked up by a fairly high quality mic).
Security researchers have successfully broken one of the most secure encryption algorithms, 4096-bit RSA, by listening – yes, with a microphone — to a computer as it decrypts some encrypted data. The attack is fairly simple and can be carried out with rudimentary hardware. The repercussions for the average computer user are minimal, but if you’re a secret agent, power user, or some other kind of encryption-using miscreant, you may want to reach for the Rammstein when decrypting your data.
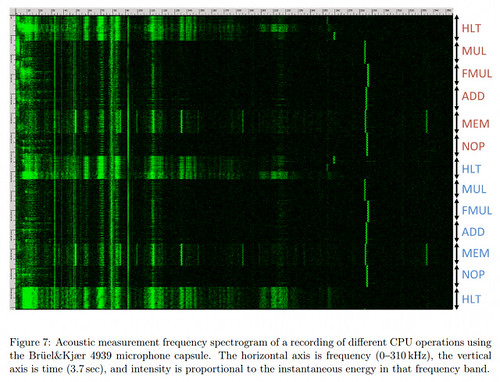
This acoustic cryptanalysis, carried out by Daniel Genkin, Adi Shamir (who co-invented RSA), and Eran Tromer, uses what’s known as a side channel attack. A side channel is an attack vector that is non-direct and unconventional, and thus hasn’t been properly secured. For example, your pass code prevents me from directly attacking your phone — but if I could work out your pass code by looking at the greasy smudges on your screen, that would be a side channel attack. In this case, the security researchers listen to the high-pitched (10 to 150 KHz) sounds produced by your computer as it decrypts data.
Interesting that one of the researchers involved in this is also a co-inventor of RSA, but that’s also a good thing – showing they are constantly trying to find ways to improve it, break it etc.
Perhaps all new encryption software will come with a feature to play some kind of white noise/music to disrupt any snooping of the high frequency CPU sounds.
Without going into too much detail, the researchers focused on a very specific encryption implementation: The GnuPG (an open/free version of PGP) 1.x implementation of the RSA cryptosystem. With some very clever cryptanalysis, the researchers were able to listen for telltale signs that the CPU was decrypting some data, and then listening to the following stream of sounds to divine the decryption key. The same attack would not work on different cryptosystems or different encryption software — they’d have to start back at the beginning and work out all of the tell-tale sounds from scratch.
The researchers successfully extracted decryption keys over a distance of four meters (13 feet) with a high-quality parabolic microphone. Perhaps more intriguingly, though, they also managed to pull of this attack with a smartphone placed 30 centimeters (12 inches) away from the target laptop. The researchers performed the attack on different laptops and desktops, with varying levels of success. For what it’s worth, the same kind of electrical data can also be divined from many other sources — the power socket on the wall, the remote end of an Ethernet cable, or merely by touching the computer (while measuring your body’s potential relative to the room’s ground potential).
Thankfully it’s a very academic type of attack and doesn’t have much of a real world implication on the majority of folks, the method could be constructed for other algorithms I assume – using the same technique.
But really, how many people sit around in public places decrypting sensitive documents? I don’t think there’s many.
Source: ExtremeTech
