[ad]
Now this is a VERY interesting project, as I’ve always said the majority of DoS attacks and DDoS attacks (90%+) could be stopped if all the ISP’s null routed packets which DO NOT originate from IP blocks they own, e.g. spoofed packets.
Basically the project has been established to see if you can spoof IP packets or not, and what percentage of ISPs already drop the packets.
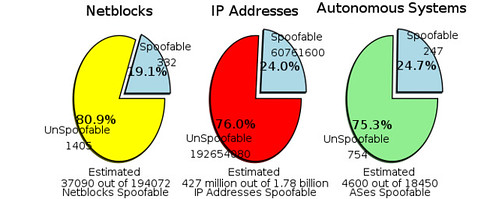
It seems in general about 20-25% of systems are able to spoof packets.
The classic design tenets of Internet architecture produced a network capable of remarkable scalability while relegating security to the end hosts. As a result, the public Internet includes no explicit notion of authenticity and will forward packets with forged headers. Malicious users capitalize on the ability to
spoof” source IP addresses for anonymity, indirection, targeted attacks and security circumvention. Compromised hosts on networks that permit IP spoofing enable a wide variety of attacks. Despite being first exploited over two-decades ago, IP spoofing is a persistent problem and a continued threat. In addition to mounting spoofed-source bandwidth-based denial-of-service (DoS) attacks, new exploits utilizing IP spoofing surface regularly.
You can read more of the intro to the ANA spoofing project here.
Some may suspect the project and the software involved is somewhat nefarious, but oh well, if you are going to get r00ted by someone, let it be MIT ok? Anyway you can always run it in a sandbox or in a fresh VMware machine.
If you don’t care either way, you can download the spoofer software here.
Please note though, it won’t run under Windows XP SP2, due to the whole raw sockets issue I would imagine.
The majority of systems tested so far have been Windows systems though (64%).
A summary of the results:
Total Completely Failed Spoof Attemps: 1823
Failed as a result of Windows XP SP2: 528
Failed as a result of (non-Windows) Operating System block: 111
Failed as a result of being Behind a NAT: 702
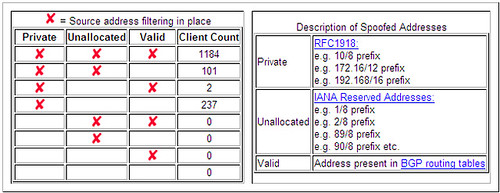
The various types of tests show which restrictions are in place.
A full summary of the results are here.

Pushkar Bhatkoti says
nMAP IS a good tool. I hvae been using it for 4 yrs and it does prety much most of spoofing stuffs.
Firewalls can be spoofed too!!